Security of SIPbased Voice over IP VoIP in enterprise networks - PowerPoint PPT Presentation
1 / 19
Title:
Security of SIPbased Voice over IP VoIP in enterprise networks
Description:
Security of SIP-based Voice over IP (VoIP) in enterprise ... Voice over IP Security Alliance (VOIPSA) in early 2005 ... However, VoIP security not utopian ... – PowerPoint PPT presentation
Number of Views:187
Avg rating:3.0/5.0
Title: Security of SIPbased Voice over IP VoIP in enterprise networks
1
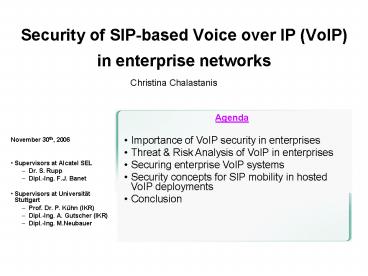
Security of SIP-based Voice over IP (VoIP) in
enterprise networks
Christina Chalastanis
- Agenda
- Importance of VoIP security in enterprises
- Threat Risk Analysis of VoIP in enterprises
- Securing enterprise VoIP systems
- Security concepts for SIP mobility in hosted VoIP
deployments - Conclusion
- November 30th, 2006
- Supervisors at Alcatel SEL
- Dr. S. Rupp
- Dipl.-Ing. F.J. Banet
- Supervisors at Universität Stuttgart
- Prof. Dr. P. Kühn (IKR)
- Dipl.-Ing. A. Gutscher (IKR)
- Dipl.-Ing. M.Neubauer
2
VoIP security in full bloom
- Voice over IP Security Alliance (VOIPSA) in early
2005 - VoIP servers and IP phones in the Top 20
Internet Security Attack Target List (SANS
Institute) in mid-November, 2006 - Massive publication in 2005 and 2006 of
- White papers
- Recommendations
- Articles
- New software tools for VoIP attacks
- Emergence of new role in enterprises VoIP
administrator
3
Importance of VoIP security in enterprise networks
- Popularity of VoIP increasing in enterprises
- Security often considered as secondary, but
fundamental - Lack of confidence of enterprises about level of
VoIP security - However, VoIP security not utopian
- Importance of thorough tailored analysis of
threats and risks - VoIP certainly target of predilection of
attackers - gt VoIP security major concern for vendors,
manufacturers, researchers, service providers
4
Threat risk analysis of VoIP in enterprise
networks
5
Hybrid model of VoIP deployment
- PBX Private Exchange Branch
IP-PBXInternet Protocol Private Exchange Branch
6
Threat analysis characterization of the VoIP
system
- PBX Private Exchange Branch
IP-PBXInternet Protocol Private Exchange Branch
7
Threat Risk analysis process
likelihood
impact
int./ext
risk
I Internal H High MMedium
MMedium-to-high
- Distinction of threats
- Network-based
- Application-based
- Wireless VoIP
- Mobility
- Assessment
- Likelihood motivation difficulty
- existing protective measures
- Risk likelihood impact
- Process
- VOIPSA Taxonomy used as a frame
- Schneier attack tree model
8
Securing enterprise VoIP systems
9
Overview of security technical solutions
- Encryption of SIP signalling stream and RTP media
stream - SIP authentication mechanisms
- SIP-aware firewalls
- SPIT prevention
- VoIP Virtual Private Networks (VPNs)
- Voice over WLAN (VoWLAN) WPA2 (802.11i standard)
- However protocols not always implemented in
products, interoperability problems, traditional
firewalls, vulnerabilities in architectures
10
Comparison of four major sets of recommendations
for VoIP security Institutions
- NIST National Institute of Standards and
Technology (USA) Security considerations for
Voice over IP systems (Jan. 2005) - BSI Federal Office for Security in Information
Technology (Germ.) VoIPsec Studie zur
Sicherheit von Voice over Internet Protocol
(Oct. 2005) - NSA National Security Agency (USA) Security
Guidance for Deploying IP Telephony Systems
(Feb. 2006) - DISA Defense Information Systems Agency
(USA)Internet Protocol Telephony Voice over
Internet Protocol Security Technical
Implementation Guide version 2 (Apr. 2006)
11
Comparison of four major sets of recommendations
for VoIP security Approaches
- Classification of recommendations
- Areas of network infrastructure (NSA)
- Critical points like physical protection,
policies for softphones, call privacy and
confidentiality, and others (DISA) - Granularity and depth
- Superficial (NIST)
- Very detailed (BSI, NSA, DISA) it depends on the
topics - Categorization of security levels
- Security levels defined by the strength of
mitigation (NSA) - Security levels defined by the vulnerability
severity they have to mitigate (DISA, BSI) - Focus on particular topics
12
Comparison of four major sets of recommendations
for VoIP security Extract (1/2)
Level of security
DISA
BSI
NIST
NSA
NM Not mentioned H High M Medium
13
Comparison of four major sets of recommendations
for VoIP security Extract (2/2)
Level of security
DISA
BSI
NIST
NSA
NM Not mentioned H High M Medium
nodisagree
14
Comparison of four major sets of recommendations
for VoIP security Results
- Points of divergence
- Subdivision of voice VLAN into further VLANs
number? - Softphones for which level of security?
- Configuration of IP phones at the terminal or
through a web interface? - Common points
- Physical protection of VoIP servers
- physically secured areas
- access only to authorized personnel
- Protection against power cuts
- Data and voice segregation
- at least, 1 voice VLAN 1 data VLAN
- Subdivision in producing VLAN and consuming
VLAN - Dedicated DHCP and AAA servers for VoIP
- VoIP network protection and internal traffic
control - Network Intrusion Detection Systems (NIDS)
connected to each switch port - L3 4 firewall between voice and data VLANs
- Call privacy and confidentiality VoIP VPNs over
the Internet
15
Application of security concepts in enterprises
16
Security concepts for SIP mobility in hosted VoIP
deployments
17
Setting the problem
18
Comparison of solutions
- Solution 1 VPN to the VoIP service provider
Solution 2 VPN to the enterprise
- Mobile workers perceived as external by hosted
IP-PBX - Possible configuration of hosted PBX to restrict
access to some services gt impact of laptop theft
lower
- Mobile workers perceived as internal by hosted
IP-PBX - Impact of laptop theft higher attacker access
all services as an internal worker - Several hops QoS of voice can be worse
19
Conclusion
- Summary
- Modelling of the VoIP migration steps in
enterprises - Identification of VoIP-specific security
requirements - Comparison of taxonomies
- Identification and classification of threats
using the Schneiers attack trees and the VOIPSA
taxonomy - Comparison of recommendations published by major
institutions - New topic security in hosted VoIP deployments
supporting mobile workers - Conclusions
- Confidentiality/Privacy Integrity/Authenticity
most important VoIP security requirements - VOIPSA Threat Taxonomy best frame for threat
analysis - DISA and NSA recommendations most helpful to
enterprises - Small enterprises ask appropriate questions to
VoIP service providers about security mechanisms
in hosted solutions - Further work
- Deeper study of the hosted VoIP deployment
supporting mobility and optimization of solutions