Strengthening Cybersecurity Effective IT Security Policies PowerPoint PPT Presentation
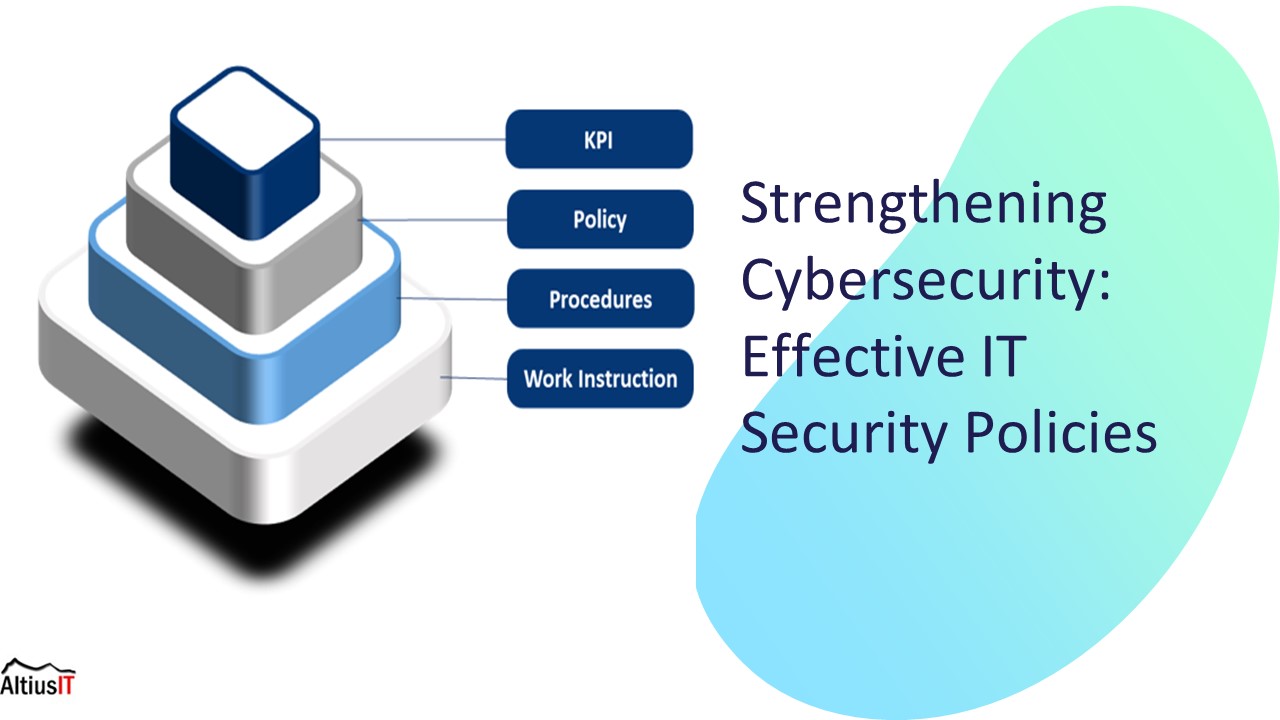
Title: Strengthening Cybersecurity Effective IT Security Policies
1
Strengthening Cybersecurity Effective IT
Security Policies
2
Introduction
- In today's digital world, cybersecurity is a
critical concern for organizations. Effective IT
security policies are essential to protect
sensitive data and prevent cyber attacks. This
presentation will discuss key strategies for
strengthening cybersecurity.
3
Understanding Cyber Threats
- Cyber threats, including malware, phishing, and
ransomware, pose significant risks to
organizations. Understanding the threat landscape
is crucial for developing robust IT security
policies.
4
Key Components of IT Security Policies
Effective IT security policies should encompass
access control, data encryption, incident
response plans, and regular security training.
These components are essential for mitigating
cybersecurity risks.
5
Implementing a Risk Management Framework
- A comprehensive risk management framework helps
organizations identify, assess, and mitigate
cybersecurity risks. This approach involves
continuous monitoring, threat intelligence, and
proactive security measures.
6
Ensuring Regulatory Compliance
- Adhering to regulatory requirements such as GDPR,
HIPAA, and PCI DSS is crucial for maintaining
data security and privacy. IT security policies
must align with these regulations to ensure
compliance.
7
Conclusion
Effective IT security policies are fundamental
for safeguarding organizations against cyber
threats. By understanding the threat landscape,
implementing robust policies, and ensuring
regulatory compliance, businesses can strengthen
their cybersecurity posture.
8
Thanks!
Do you have any questions? pnikkhesal_at_altiusit.com
(741)794-5210 https//altiusit.com/
PowerShow.com is a leading presentation sharing website. It has millions of presentations already uploaded and available with 1,000s more being uploaded by its users every day. Whatever your area of interest, here you’ll be able to find and view presentations you’ll love and possibly download. And, best of all, it is completely free and easy to use.
You might even have a presentation you’d like to share with others. If so, just upload it to PowerShow.com. We’ll convert it to an HTML5 slideshow that includes all the media types you’ve already added: audio, video, music, pictures, animations and transition effects. Then you can share it with your target audience as well as PowerShow.com’s millions of monthly visitors. And, again, it’s all free.
About the Developers
PowerShow.com is brought to you by CrystalGraphics, the award-winning developer and market-leading publisher of rich-media enhancement products for presentations. Our product offerings include millions of PowerPoint templates, diagrams, animated 3D characters and more.