Final Exam Monday May 16, 6:008:30 pm normal class time PowerPoint PPT Presentation
1 / 46
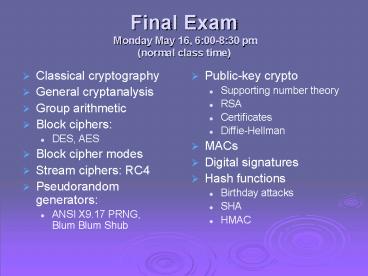
Title: Final Exam Monday May 16, 6:008:30 pm normal class time
1
Final Exam Monday May 16, 600-830 pm (normal
class time)
- Classical cryptography
- General cryptanalysis
- Group arithmetic
- Block ciphers
- DES, AES
- Block cipher modes
- Stream ciphers RC4
- Pseudorandom generators
- ANSI X9.17 PRNG, Blum Blum Shub
- Public-key crypto
- Supporting number theory
- RSA
- Certificates
- Diffie-Hellman
- MACs
- Digital signatures
- Hash functions
- Birthday attacks
- SHA
- HMAC
2
Final Exam continued
- Key exchange
- Session keys
- Authentication protocols
- Network layer
- Anti-replay techniques
- Needham-Schroeder
- Woo-Lam
- Forward secrecy
- Long term vs short term
- SSH
- Authentication
- SSL / TLS
- Handshake
- Authentication
- Rupdate projects
- Design, not implementation
- Choices made
- Pros and cons
- What's missing?
- Includes all assigned reading
- Closed book and notes
- I will provide technical details
3
802.11, WEP, 802.1xCase Study
- Lecture Notes for 91.561UMass Lowell Computer
ScienceDavid Martin
4
Orientation
- Miraculously, free downloads available
- IEEE 802 Overview Architecture
- IEEE 802.1 Bridging Management
- IEEE 802.2 Logical Link Control
- IEEE 802.3 CSMA/CD Access Method
- IEEE 802.5 Token Ring Access Method
- IEEE 802.11 Wireless
- IEEE 802.12 Demand Priority Access
- IEEE 802.15 Wireless Personal Area Networks
- IEEE 802.16 Broadband Wireless Metropolitan
Area Networks
5
Recommended References
- Real 802.11 Security Wi-Fi Protected Access and
802.11i, Edney and Arbaugh, Addison-Wesley, 2003 - Wi-Foo The Secrets of Wireless Hacking,
Vladimirov, Gavrilenko and Mikhailovsky,
Addison-Wesley, 2004
6
Orientation
- IEEE 802.11
- Late 90s wireless networking
- 802.11 1999, base wireless spec
- WEP is defined here
- 802.11a 1999, 5 GHz, 1 and 2 Mb/s
- 802.11b 1999, 2.4 GHz, 5.5 and 11 Mb/s
- 802.11g 2003, 2.4 GHz, 54 Mb/s
- 802.11n 2008?, 2.4 GHz, 540 Mb/s
- 802.11i (RSN addendum) 2004
- IEEE 802.1
- 802.1d bridging
- 802.1q virtual LANs
- 802.1x (2001, 2004) port-based access control
- Much of this presentation text is taken from
these standards - WiFi
- Industry association trying to achieve
interoperability - Trademark protection of WiFi logo
7
802.11 Wireless
- Individual cells are called basic service sets
(BSS) - BSS can be combined by distribution systems (DS)
into extended service sets (ESS) - Like how individual wired LANs can be combined
into an extended LAN via bridging
8
Complete Picture
Source IEEE 802.11 standard
9
(No Transcript)
10
Connecting to 802.11 LAN
- Three types of transmissions
- Management
- Control (media sharing)
- Data
- Each wireless station has its own MAC address
- SSID a network's name (service set ID)
- Can be overlapping sensible for creating
extended LAN - APs run over (small) numeric channels that
correspond to frequencies in the given range - Probe request response
- For determining which APs are accessible
- Passive variant also possible beacons
- Can learn published SSIDs, associated parameters
11
802.11 Authentication
- If desired, an IEEE 802.11 network may be
operated using Open System authentication. This
may violate implicit assumptions made by higher
network layers. In an Open System, any station
may become authenticated. - In other words, no authentication required
- IEEE 802.11 also supports Shared Key
authentication. Use of this authentication
mechanism requires implementation of the wired
equivalent privacy (WEP) option. In a Shared Key
authentication system, identity is demonstrated
by knowledge of a shared, secret, WEP encryption
key.
12
802.11 Association
- Association required in order to transmit through
an AP to anywhere - Once associated, the extended network can route
transmissions to appropriate AP - Authentication happens before association
- Management messages
- Association / reassociation request response
13
802.11 Transmission
- CSMA / CA
- Carrier sense multiple access / collision
avoidance - Transmissions are ACKed
- Otherwise you don't know if your frame was
received there's no reliable collision detection - Request to send / clear to send also possible but
not required - CTS presumably can be heard by each station able
to cause a collision - These extra messages are in the "control"
category
14
802.11 Layering
15
MAC Frame Layout
- Note long frame body
- 4 Addresses depending on frame type, could
include - Service set ID
- Destination, Source
- Receiver, Transmitter current hop within
extended service set - Frame control field
16
Message types
17
Message types
18
802.11 Privacy (Confidentiality)
- From IEEE 802.11 standard, Section 5.4.3.3
- In a wired LAN, only those stations physically
connected to the wire may hear LAN traffic. Not
so with a wireless shared medium. - IEEE 802.11 specifies an optional privacy
algorithm, WEP, that is designed to satisfy the
goal of wired LAN equivalent privacy. The
algorithm is not designed for ultimate security
but rather to be at least as secure as a wire. - IEEE 802.11 uses the WEP mechanism to perform the
actual encryption of messages. Note that privacy
may only be invoked for data frames and some
Authentication Management frames. - All stations initially start in the clear in
order to set up the authentication and privacy
services. - The default privacy state for all IEEE 802.11
STAs is in the clear. If the privacy service is
not invoked, all messages shall be sent
unencrypted.
19
Desired Properties of WEP
- It is reasonably strong
- The security afforded by the algorithm relies on
the difficulty of discovering the secret key
through a brute-force attack. This in turn is
related to the length of the secret key and the
frequency of changing keys. WEP allows for the
changing of the key and frequent changing of the
IV. - It is self-synchronizing
- WEP is self-synchronizing for each message. This
property is critical for a data-link level
encryption algorithm, where best effort
delivery is assumed and packet loss rates may be
high. - It is efficient
- The WEP algorithm is efficient and may be
implemented in either hardware or software. - It may be exportable
- ... However, due to the legal and political
climate toward cryptography at the time of
publication, no guarantee can be made that any
specific IEEE 802.11 implementations that use WEP
will be exportable from the USA. - It is optional
- The implementation and use of WEP is an IEEE
802.11 option.
20
WEP Design
- About 4 pages of 802.11 specification
- Encryption via stream cipher
- PRNG is RC4
- Integrity algorithm is CRC-32
21
WEP Design
Note the encypherment process has expanded the
original Frame Body by 8 octets, 4 for the IV
field and 4 for the ICV. The ICV is calculated
on the data field only.
22
RC4 Reminder
- From Fluhrer et al paper
23
IV in Stream Cipher
- Normally don't think of initialization vectors in
stream ciphers they just take a key and generate
a byte at a time - Also true in this case IV is completely
specified outside of RC4 - Used to ensure that retransmission of same
plaintext will look different - ( IV WEP key ) is used as RC4 key
24
WEP as Foundation for
- Authentication
- Initial assurance of identity
- Binding authentication to session
- Mutual authentication
- Subkey generation
- Integrity protection
- Message modification detection
- Replay detection
- Confidentiality
- Message privacy
- Key privacy
25
Authentication
- "Open" authentication takes one round trip to
negotiate and doesn't do much - Otherwise, "Shared key" authentication between
Client and Access Point - C gt AP "Want shared authentication"
- AP gt C 128-byte challenge
- challenge must not be static
- C gt AP WEP( challenge ) using shared key
- AP gt C approve/deny
26
Analysis
- Nothing from authentication procedure persists
into subsequent transmissions - No ongoing session authentication
- No subkey generation
- No (mutual) authentication of AP to client
- Note that client chooses IV when transmitting
response - Attacker Eve eavesdrops on one challenge/response
- Plaintext, ciphertext, and IV are known can
recover keystream used in that transmission with
XOR - Then to authenticate herself, she reuses the IV
and recovered keystream to encrypt an arbitrary
challenge
27
WEP as Foundation for
- Authentication
- Initial assurance of identity
- Binding authentication to session
- Mutual authentication
- Subkey generation
- Integrity protection
- Message modification detection
- Replay detection
- Confidentiality
- Message privacy
- Key privacy
28
Integrity Protection
- After authentication phase, using WEP to protect
the data - Integrity protection value is CRC-32, not a hash
function - WEP uses a stream cipher
- So, flip bit n of ciphertext and adjust plaintext
CRC to compensate - Not very good protection at all
- Replay detection
- None!
29
WEP as Foundation for
- Authentication
- Initial assurance of identity
- Binding authentication to session
- Mutual authentication
- Subkey generation
- Integrity protection
- Message modification detection
- Replay detection
- Confidentiality
- Message privacy
- Key privacy
30
Confidentiality Message Privacy
- Constant WEP key constant IV same keystream
each time - If Eve knows IV plaintext ciphertext then she
knows the keystream for that IV - Or if she knows IV ciphertext1 ciphertext2
difference - Generally, WEP keys are long-term
- Hard to change, that's why you configure 4 of
them - So IV shouldn't be constant
- 802.11 standard doesn't require change, but
(most) everyone does change it per frame
31
So change the IV
- IV is 24 bits max 16,777,216 values
- Choose randomly?
- Birthday paradox expect reuse after 212 4096
transmissions - So increment instead
- 11 Mb/s, you can get about 500 full frames / s
- After about 9 hours your IVs will wrap around at
this rate - 1500 bytes per IV can write them all down in 23
Gb - Note that since most stations use same key, you
don't have to attack any particular transmitter - All in all, very leaky, even when you never learn
the key - Borisov, Goldberg, Wagner give more specific
attacks in "Intercepting Mobile Communications
Insecurity of 802.11", Mobicom 2001
32
Attacking the Key
- Fluhrer, Mantin, Shamir 2001 "Weaknesses in the
Key Scheduling Algorithm of RC4", Eighth Annual
Workshop on Selected Areas in Cryptography - "IV Weakness" When part of the RC4 key is known,
the unknown part can sometimes be derived from
the keystream - Easiest when known part precedes unknown part
- ( IV WEP key ) RC4 key
33
Attacking the Key
- Time to recover bytes of the key is linear in
length of key, not exponential - Stubblefield, Ioannidis, Rubin implemented attack
and described in "Using the Fluhrer, Mantin,
Shamir Attack to break WEP", Symposium on Network
and Distributed System Security 2002. - They could recover the key after about 5,000,000
packets - Various recommendations
- don't use WEP
- to resist IV attack, make RC4 key be a "secure
hash" of IV using secret key rather than just (
IV secret key ) - throw away first 256 bytes of keystream to resist
another type of attack - wepcrack, aircrack, airsnort, weplab, etc.
34
More recent attacks
- Tews, Weinmann, Pyshkin 2007 Breaking 104-bit WEP
in Less Than 60 Seconds - Based on Klein's 2005 attacks on RC4
- ARP produces known keystream
- Spoofing deauthentications generates more
- WEP usage stats from "central Germany"
35
WEP as Foundation for
- Authentication
- Initial assurance of identity
- Binding authentication to session
- Mutual authentication
- Subkey generation
- Integrity protection
- Message modification detection
- Replay detection
- Confidentiality
- Message privacy
- Key privacy
36
Improvements Future
- TKIP Temporal Key Integrity Protocol
- Designed to allow many older WEP devices to be
upgraded to a secure protocol. Includes - Integrity check 20-bit "Michael" mandatory
countermeasures - Avoiding weak IVs
- Anti-replay
- Avoiding IV reuse
- Automatic per-packet key update to avoid FMS
attack - "TKIP is a masterpiece of retro-engineering and
provides real security in a way that WEP never
could. All the major weaknesses of WEP have been
addressed... " - wrote Edney and Arbaugh in Real 802.11 Security
37
Dynamic WEP
- "The key is provided for me automatically"
(checkbox in Windows) - Simple patch to change keys over time to avoid
FMS attacks - Forces clients to reauthenticate after a timeout
(e.g. 60 minutes) - A faint shadow of TKIP/WPA, though supported by
many vendors
38
Improvements Future
- 802.11i a workable spec for wireless security
- RSN Robust Security Network
- Main mode is AES-CCMP Counter ModeCBC MAC
Protocol - Designed cleanly for new hardware
- Includes key exchange based on long-term secrets
- TKIP is a legacy mode under RSN
- WiFi alliance
- Industry group didn't want to wait
- Tore out TKIP and 802.1x EAP, naming it
- WPA WiFi Protected Access
- Later, WPA2 named for 802.11i
39
802.1x
- "Port-based Network Access Control"
- 2001 and 2004 standards
- Looking for better mechanism than MAC filtering
40
802.1x Central Idea
- Supplicant wants to use a LAN port (PAE)
- Uses 802.1x Extensible Authentication Protocol
(EAP) - EAP is from PPP
- Authentication server uses Remote Access Dial-in
User Service (RADIUS)
41
802.1x
- Recall 802.11 authentication precedes association
- Supplicant will engage in EAP session with access
point before associating - EAP Extensible Authentication Protocol
- Supports TLS, PEAP, SecureID, RSA, MS-CHAPv2,etc.
- Problem physical port swapping assumed to be
unlikely, but wireless hijacking is comparatively
easy - Mishra and Arbaugh described session hijacking
and man-in-middle attacks (2001) - Quite practical in unencrypted session
42
802.1x continued
- Microsoft invented MS-MPPE-Recv-Key attribute in
order to deliver session key for their
Point-to-Point Encryption protocol (their own VPN
technology) - Adopted in WPA I don't know about 802.11i
- EAP is not done confidentially
- User identification sent in clear
- Server responses can be spoofed!
43
EAP options
- EAPTLS widely supported on wireless clients and
RADIUS servers - uses public key certificates to authenticate both
the wireless clients and the RADIUS servers by
establishing an encrypted TLS session between the
two. - PEAP "Protected" EAP
- Phase 1 client performs simple EAP but may use
anonymous identifier - Establishes session key for encryption
integrity - Phase 2 client performs normal EAP within
established tunnel, now sending its real
authenticator
44
EAP options
- TTLS two stages, similar to PEAP
- uses a TLS session to protect tunneled client
authentication - can also use nonEAP authentication protocols
such as CHAP, MSCHAP, etc. - LEAP "Lightweight", proprietary Cisco protocol
45
UML Implementation
- Intended to support Windows, Mac, Linux
- 802.1x PEAP with MS-CHAPv2
- MS-CHAPv2 RFC 2759
- straightforward challenge-response proving
knowledge of username password - appears to require WPA AES now, though was
using TKIP previously (and dynamic WEP before
that)
46
Virtual Private Networks
- VPNs may allow you to ignore layer 2
- Wireless station connected to VPN
- Pros
- Confidentiality, integrity, etc.
- Cons
- Denial of Service is still easy
- Wireless stations may still respond to non-VPN
wireless traffic - For example, hotspotvpn.com