David Fordham PowerPoint PPT Presentation
Title: David Fordham
1
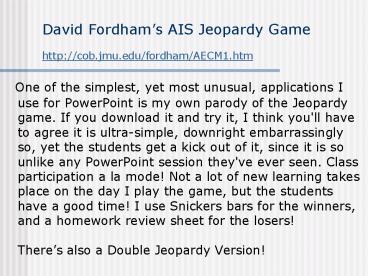
David Fordhams AIS Jeopardy Game
http//cob.jmu.edu/fordham/AECM1.htm
- One of the simplest, yet most unusual,
applications I use for PowerPoint is my own
parody of the Jeopardy game. If you download it
and try it, I think you'll have to agree it is
ultra-simple, downright embarrassingly so, yet
the students get a kick out of it, since it is so
unlike any PowerPoint session they've ever seen.
Class participation a la mode! Not a lot of new
learning takes place on the day I play the game,
but the students have a good time! I use Snickers
bars for the winners, and a homework review sheet
for the losers!Theres also a Double Jeopardy
Version!
2
ACTG 313
- November 17, 2006
- Professor David Fordham
- James Madison University
- Jeopardy Game PowerPoint Files can be downloaded
from http//cob.jmu.edu/fordham/AECM1.htm
3
ACTG 313 Jeopardy
4
Todays Categories
- Transaction Cycles
- Internal Control
- Information Security
- Connectors
- Flowcharting
- Miscellaneous
5
TransnCycles
Con-nectors
Flow Chart
Misc
Info Security
InternalControl
100
100
100
100
100
100
200
200
200
200
200
200
300
300
300
300
300
300
400
400
400
400
400
400
500
500
500
500
500
500
6
Transaction Cycles 100
Check-writing is a major activity towards the end
of this cycle.
What is the Purchasing/Payables/Disbursements
cycle?
Back to Board
7
Transaction Cycles 200
Preparation of a Deposit Slip is an activity
towards the end of this transaction cycle.
What is the Sales/Billing/Cash-Receipts cycle?
Back to Board
8
Transaction Cycles 300
This form is a legal document creating a bailment
giving a third-party transportation company
permission to be in possession of your companys
merchandise (or that of your customer) for the
purpose of delivery.
What is a Bill of Lading?
Back to Board
9
Transaction Cycles 400
Although not necessarily a true transaction in
that it does not involve parties outside a
company, this is generally referred to as one of
the common transaction cycles because of its
complexity and the large number of
information-related activities often taking place
in its course.
What is the Manufacturing Cycle?
Back to Board
10
Transaction Cycles 500
This is a major accounting activity, typically
done monthly, and comprising an extremely
important internal control towards the end of
BOTH the purchasing AND the sales cycles.
What is the Bank Reconciliation?
Back to Board
11
Internal Control -- 100
This is the formal name of the group whose
initials are C.O.S.O.
What is the Committee of Sponsoring Organizations?
Back to Board
12
Internal Control -- 200
The three functions of controls are Correction,
Detection, and this.
What is Prevention?
Back to Board
13
Internal Control -- 300
SAS number 78 is addressed to this audience.
Who are Financial (or Independent) Auditors?
Back to Board
14
Internal Control -- 400
This classic piece of Congressional legislation
was the first to specifically state that
management of all publicly-held companies is
responsible for implementing internal control
in corporate reporting systems.
What is the Foreign Corrupt Practices Act?
Back to Board
15
Internal Control -- 500
The names of the two U.S. Congressmen who
sponsored the federal legislation addressing
corporate governance, and mandating the personal
responsibility of management for the review of
the internal control system.
Who are Sarbanes and Oxley?
Back to Board
16
Information Security 100
This is the third Information Security pillar,
along with Data Confidentiality and Data
Integrity.
What is Data Availability?
Back to Board
17
Information Security 200
A smoke alarm is an example of this kind of
countermeasure.
What are Detective Countermeasures?
Back to Board
18
Information Security 300
DAILY DOUBLE!!!
19
Information Security 400
The Triad of Information Security pillars share
this acronym with a internationally famous (or
infamous) U.S. government agency.
What is C.I.A.?
Back to Board
20
Information Security 500
To avoid reduce the likelihood of modification to
computer programs, a good SDLC team will use this
kind of programming language in their development
project.
What is a compiled language?
Back to Board
21
Connectors 100
What is an HP Power Connector?
Back to Board
22
Connectors 200
What is a Phone plug?
Back to Board
23
Connectors 300
What is an RCA or phono plug?
Back to Board
24
Connectors 400
8 contacts per plug
What is an RJ-45 plug?
Back to Board
25
Connectors 500
What is a DB-9 connector?
Back to Board
26
Flowcharting 100
What is the symbol for Data Storage, or a Data
File?
Back to Board
27
Flowcharting 200
What is the symbol for a manual process?
Back to Board
28
Flowcharting 300
What is the symbol for an off-page connector?
Back to Board
29
Flowcharting 400
What is the symbol for a PREDEFINED process?
Back to Board
30
Flowcharting 500
What is the symbol for computer Input/Output?
Back to Board
31
Miscellaneous 100
The gender of this connector.
What is female?
Back to Board
32
Miscellaneous 200
The three-letter acronym representing the field
of study addressing the concepts, design, and
evaluation of comprehensive information systems
which gather, store, analyze, and report
accounting and financial data.
What is AIS?
Back to Board
33
Miscellaneous 300
The full name of the 15th-century Venetian
(1445-1517) who in 1494 published his influential
treatise Summa de Arithmetica, Geometria,
Proportioni et Proportionalita describing
double-entry bookkeeping, including debits,
credits, journals, ledgers, and financial
statements. (He later became a Franciscan monk.)
Who is Luca Pacioli?
Back to Board
34
Miscellaneous 400
Bill McCarthys REA model was based on George
Sorters Events Approach to accounting, and
incorporates this concept from Theoretical
Philosophy, which refers to the use of symbols to
represent real world entities, events, and
processes.
What is Semantic Modeling?
Back to Board
35
Miscellaneous 500
Under the COSO 1992 framework, this is the fifth
component of Internal Control, the other four
being Control Environment, Risk Analysis, Control
Activities, and Information/ Communication.
What is Monitoring?
Back to Board
36
Information Security ---
Specify your wager
37
Information Security
When these two match up and get together, an
incident occurs, not necessarily a loss.
What are a Threat and Vulnerability?
Back to Board
38
Information Security --
Specify your wager
39
Information Security ---
What are Authentication and Non-Repudiation?
Back to Board
40
Final Jeopardy
The category is IT Auditing
41
IT Auditing
Specify your Wagers
42
IT Auditing
- The two primary assessment activities found in an
IT audit.