Semesters 1 - PowerPoint PPT Presentation
Title:
Semesters 1
Description:
Title: Where Have We Been? Author: Allan P. Johnson Last modified by: RZ Created Date: 12/20/2000 12:29:13 AM Document presentation format: On-screen Show – PowerPoint PPT presentation
Number of Views:45
Avg rating:3.0/5.0
Title: Semesters 1
1
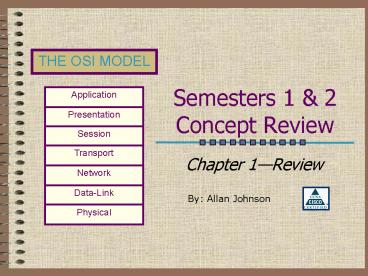
Semesters 1 2Concept Review
- Chapter 1Review
By Allan Johnson
2
Table of Contents
- Review the OSI Model
- LAN Devices Technologies
- IP Addressing
- CIDR Notation
- Routing
- Transport Layer
Go There!
Go There!
Go There!
Go There!
Go There!
Go There!
3
Arhitectura generala a Internetului
4
Arhitectura Internet - 2
5
Componente Internet
6
Protocol de retea - definitie
- un protocol defineste formatul si ordinea
mesajelor schimbate între doua sau mai multe
entitati ce comunica între ele, precum si
actiunile ce sunt întreprinse odata cu
transmiterea sau receptia unui mesaj sau a unui
alt eveniment.
7
Review The Model
- Open Systems Interconnected Reference Model
Table of Contents
8
Why A Layered Model?
- Reduces complexity
- Standardizes interfaces
- Facilitates modular engineering
- Ensures interoperable technology
- Accelerates evolution
- Simplifies teaching learning
Application
Presentation
Session
Transport
Network
Data-Link
Physical
9
Application Layer
- Provides network services (processes) to
applications. - For example, a computer on a LAN can save files
to a server using a network redirector supplied
by NOSs like Novell. - Network redirectors allow applications like Word
and Excel to see the network.
Application
Presentation
Session
Transport
Network
Data-Link
Physical
10
Presentation Layer
- Provides data representation and code formatting.
- Code formatting includes compression and
encryption - Basically, the presentation layer is responsible
for representing data so that the source and
destination can communicate at the application
layer.
Application
Presentation
Session
Transport
Network
Data-Link
Physical
11
Session Layer
- Provides inter-host communication by
establishing, maintaining, and terminating
sessions. - Session uses dialog control and dialog separation
to manage the session - Some Session protocols
- NFS (Network File System)
- SQL (Structured Query Language)
- RCP (Remote Call Procedure)
- ASP (AppleTalk Session Protocol)
- SCP (Session Control Protocol)
- X-window
Application
Presentation
Session
Transport
Network
Data-Link
Physical
12
Transport Layer
- Provides reliability, flow control, and error
correction through the use of TCP. - TCP segments the data, adding a header with
control information for sequencing and
acknowledging packets received. - The segment header also includes source and
destination ports for upper-layer applications - TCP is connection-oriented and uses windowing.
- UDP is connectionless. UDP does not acknowledge
the receipt of packets.
Application
Presentation
Session
Transport
Network
Data-Link
Physical
13
Network Layer
- Responsible for logically addressing the packet
and path determination. - Addressing is done through routed protocols such
as IP, IPX, AppleTalk, and DECnet. - Path Selection is done by using routing protocols
such as RIP, IGRP, EIGRP, OSPF, and BGP. - Routers operate at the Network Layer
Application
Presentation
Session
Transport
Network
Data-Link
Physical
14
Data-Link Layer
- Provides access to the media
- Handles error notification, network topology
issues, and physically addressing the frame. - Media Access Control through either...
- Deterministictoken passing
- Non-deterministicbroadcast topology (collision
domains) - Important concept CSMA/CD
Application
Presentation
Session
Transport
Network
Data-Link
Physical
15
Physical Layer
- Provides electrical, mechanical, procedural and
functional means for activating and maintaining
links between systems. - Includes the medium through which bits flow.
Media can be... - CAT 5 cable
- Coaxial cable
- Fiber Optics cable
- The atmosphere
Application
Presentation
Session
Transport
Network
Data-Link
Physical
16
Peer-to-Peer Communications
- Peers communicate using the PDU of their layer.
For example, the network layers of the source and
destination are peers and use packets to
communicate with each other.
17
Encapsulation Example
- You type an email message. SMTP takes the data
and passes it to the Presentation Layer. - Presentation codes the data as ASCII.
- Session establishes a connection with the
destination for the purpose of transporting the
data.
Application
Presentation
Session
Transport
Network
Data-Link
Physical
18
Encapsulation Example
- Transport segments the data using TCP and hands
it to the Network Layer for addressing - Network addresses the packet using IP.
- Data-Link then encaps. the packet in a frame and
addresses it for local delivery (MACs) - The Physical layer sends the bits down the wire.
Application
Presentation
Session
Transport
Network
Data-Link
Physical
19
LAN Devices Technologies
- The Data-Link Physical Layers
Data-Link
Physical
Table of Contents
20
Devices
- What does it do?
- Connects LAN segments
- Filters traffic based on MAC addresses and
- Separates collision domains based upon MAC
addresses.
What layer device?
21
Devices
- What does it do?
- Since it is a multi-port bridge, it can also
- Connect LAN segments
- Filter traffic based on MAC addresses and
- Separate collision domains
- However, switches also offer full-duplex,
dedicated bandwidth to segments or desktops.
What layer device?
22
Devices
- What does it do?
- Concentrates LAN connections from multiple
devices into one location - Repeats the signal (a hub is a multi-port
repeater)
What layer device?
23
Devices
- What does it do?
- Interconnects networks and provides broadcast
control - Determines the path using a routing protocol or
static route - Re-encapsulates the packet in the appropriate
frame format and switches it out the interface - Uses logical addressing (i.e. IP addresses) to
determine the path
What layer device?
24
Media Types
25
LAN Technologies
Three Most Common Used Today in Networking
26
Ethernet/802.3
- Cable Specifications
- 10Base2
- Called Thinnet uses coax
- Max. distance 185 meters (almost 200)
- 10Base5
- Called Thicknet uses coax
- Max. distance 500 meters
- 10BaseT
- Uses Twisted-pair
- Max. distance 100 meters
- 10 means 10 Mbps
27
Ethernet/802.3
- Ethernet is broadcast topology.
- What does that mean?
- Every devices on the Ethernet segment sees every
frame. - Frames are addressed with source and destination
______ addresses. - When a source does not know the destination or
wants to communicate with every device, it
encapsulates the frame with a broadcast MAC
address FFFF.FFFF.FFFF - What is the main network traffic problem caused
by Ethernet broadcast topologies?
28
Ethernet/802.3
- Ethernet topologies are also shared media.
- That means media access is controlled on a first
come, first serve basis. - This results in collisions between the data of
two simultaneously transmitting devices. - Collisions are resolved using what method?
29
Ethernet/802.3
- CSMA/CD (Carrier Sense Multiple Access with
Collision Detection) - Describe how CSMA/CD works
- A node needing to transmit listens for activity
on the media. If there is none, it transmits. - The node continues to listen. A collision is
detected by a spike in voltage (a bit can only be
a 0 or a 1--it cannot be a 2) - The node generates a jam signal to tell all
devices to stop transmitting for a random amount
of time (back-off algorithm). - When media is clear of any transmissions, the
node can attempt to retransmit.
30
Address Resolution Protocol
- In broadcast topologies, we need a way to resolve
unknown destination MAC addresses. - ARP is protocol where the sending device sends
out a broadcast ARP request which says, Whats
you MAC address? - If the destination exists on the same LAN segment
as the source, then the destination replies with
its MAC address. - However, if the destination and source are
separated by a router, the router will not
forward the broadcast (an important function of
routers). Instead the router replies with its
own MAC address.
31
IP Addressing
- Subnetting Review
Network
Table of Contents
32
Logical Addressing
- At the network layer, we use logical,
hierarchical addressing. - With Internet Protocol (IP), this address is a
32-bit addressing scheme divided into four
octets. - Do you remember the classes 1st octets value?
- Class A 1 - 126
- Class B 128 - 191
- Class C 192 - 223
- Class D 224 - 239 (multicasting)
- Class E 240 - 255 (experimental)
33
Network vs. Host
Class A 27 126 networks 224 gt 16 million
hosts
Class B 214 16,384 networks 216 gt 65,534
hosts
Class C 221 gt 2 million networks 28 254
hosts
34
Why Subnet?
- Remember we are usually dealing with a broadcast
topology. - Can you imagine what the network traffic overhead
would be like on a network with 254 hosts trying
to discover each others MAC addresses? - Subnetting allows us to segment LANs into logical
broadcast domains called subnets, thereby
improving network performance.
35
Four Subnetting Steps
- To correctly subnet a given network address into
subnet addresses, ask yourself the following
questions - How many bits do I need to borrow?
- Whats the subnet mask?
- Whats the magic number or multiplier?
- What are the first three subnetwork addresses?
- Lets look at each of these questions in detail
36
1. How many bits to borrow?
- First, you need to know how many bits you have to
work with. - Second, you must know either how many subnets you
need or how many hosts per subnet you need. - Finally, you need to figure out the number of
bits to borrow.
37
1. How many bits to borrow?
- How many bits do I have to work with?
- Depends on the class of your network address.
- Class C 8 host bits
- Class B 16 host bits
- Class A 24 host bits
- Remember you must borrow at least 2 bits for
subnets and leave at least 2 bits for host
addresses. - 2 bits borrowed allows 22 - 2 2 subnets
38
1. How many bits to borrow?
- How many subnets or hosts do I need?
- A simple formula
- Total Bits Bits Borrowed Bits Left
- TB BB BL
- I need x subnets
- I need x hosts
- Remember we need to subtract two to provide for
the subnetwork and broadcast addresses.
39
1. How many bits to borrow?
- Class C Example 210.93.45.0
- Design goals specify at least 5 subnets so how
many bits do we borrow? - How many bits in the host portion do we have to
work with (TB)? - Whats the BB in our TB BB BL formula? (8
BB BL) - 2 to the what power will give us at least 5
subnets? - 23 - 2 6 subnets
40
1. How many bits to borrow?
- How many bits are left for hosts?
- TB BB BL
- 8 3 BL
- BL 5
- So how many hosts can we assign to each subnet?
- 25 - 2 30 hosts
41
1. How many bits to borrow?
- Class B Example 185.75.0.0
- Design goals specify no more than 126 hosts per
subnet, so how many bits do we need to leave
(BL)? - How many bits in the host portion do we have to
work with (TB)? - Whats the BL in our TB BB BL formula? (16
BB BL) - 2 to the what power will insure no more than 126
hosts per subnet and give us the most subnets? - 27 - 2 126 hosts
42
1. How many bits to borrow?
- How many bits are left for subnets?
- TB BB BL
- 16 BB 7
- BL 9
- So how many subnets can we have?
- 29 - 2 510 subnets
43
2. Whats the subnet mask?
- We determine the subnet mask by adding up the
decimal value of the bits we borrowed. - In the previous Class C example, we borrowed 3
bits. Below is the host octet showing the bits we
borrowed and their decimal values.
We add up the decimal value of these bits and get
224. Thats the last non-zero octet of our
subnet mask.
So our subnet mask is 255.255.255.224
44
3. Whats the magic number?
- To find the magic number or the multiplier we
will use to determine the subnetwork addresses,
we subtract the last non-zero octet from 256. - In our Class C example, our subnet mask was
255.255.255.224. 224 is our last non-zero octet. - Our magic number is 256 - 224 32
45
Last Non-Zero Octet
- Memorize this table. You should be able to
- Quickly calculate the last non-zero octet when
given the number of bits borrowed. - Determine the number of bits borrowed given the
last non-zero octet. - Determine the amount of bits left over for hosts
and the number of host addresses available.
46
4. What are the subnets?
- We now take our magic number and use it as a
multiplier. - Our Class C address was 210.93.45.0.
- We borrowed bits in the fourth octet, so thats
where our multiplier occurs - 1st subnet 210.93.45.32
- 2nd subnet 210.93.45.64
- 3rd subnet 210.93.45.96
- We keep adding 32 in the fourth octet to get all
six available subnet addresses.
47
Host Broadcast Addresses
- Now you can see why we subtract 2 when
determining the number of host address. - Lets look at our 1st subnet 210.93.45.32
- What is the total range of addresses up to our
next subnet, 210.93.45.64? - 210.93.45.32 to 210.93.45.63 or 32 addresses
- .32 cannot be assigned to a host. Why?
- .63 cannot be assigned to a host. Why?
- So our host addresses are .33 - .62 or 30 host
addresses--just like we figured out earlier.
48
CIDR Notation
- A Different Way to Represent a Subnet Mask
Network
Table of Contents
49
CIDR Notation
- Classless Interdomain Routing is a method of
representing an IP address and its subnet mask
with a prefix. - For example 192.168.50.0/27
- What do you think the 27 tells you?
- 27 is the number of 1 bits in the subnet mask.
Therefore, 255.255.255.224 - Also, you know 192 is a Class C, so we borrowed 3
bits!! - Finally, you know the magic number is 256 - 224
32, so the first useable subnet address is
197.168.50.32!! - Lets see the power of CIDR notation.
50
202.151.37.0/26
- Subnet mask?
- 255.255.255.192
- Bits borrowed?
- Class C so 2 bits borrowed
- Magic Number?
- 256 - 192 64
- First useable subnet address?
- 202.151.37.64
- Third useable subnet address?
- 64 64 64 192, so 202.151.37.192
51
198.53.67.0/30
- Subnet mask?
- 255.255.255.252
- Bits borrowed?
- Class C so 6 bits borrowed
- Magic Number?
- 256 - 252 4
- Third useable subnet address?
- 4 4 4 12, so 198.53.67.12
- Second subnets broadcast address?
- 4 4 4 - 1 11, so 198.53.67.11
52
200.39.89.0/28
- What kind of address is 200.39.89.0?
- Class C, so 4 bits borrowed
- Last non-zero octet is 240
- Magic number is 256 - 240 16
- 32 is a multiple of 16 so 200.39.89.32 is a
subnet address--the second subnet address!! - Whats the broadcast address of 200.39.89.32?
- 32 16 -1 47, so 200.39.89.47
53
194.53.45.0/29
- What kind of address is 194.53.45.26?
- Class C, so 5 bits borrowed
- Last non-zero octet is 248
- Magic number is 256 - 248 8
- Subnets are .8, .16, .24, .32, ect.
- So 194.53.45.26 belongs to the third subnet
address (194.53.45.24) and is a host address. - What broadcast address would this host use to
communicate with other devices on the same
subnet? - It belongs to .24 and the next is .32, so 1 less
is .31 (194.53.45.31)
54
No Worksheet Needed!
- After some practice, you should never need a
subnetting worksheet again. - The only information you need is the IP address
and the CIDR notation. - For example, the address 221.39.50/26
- You can quickly determine that the first subnet
address is 221.39.50.64. How? - Class C, 2 bits borrowed
- 256 - 192 64, so 221.39.50.64
- For the rest of the addresses, just do multiples
of 64 (.64, .128, .192).
55
The Key!!
- MEMORIZE THIS TABLE!!!
56
Practice On Your Own
- Below are some practice problems. Take out a
sheet of paper and calculate... - Bits borrowed
- Last non-zero octet
- Second subnet address and broadcast address
- 192.168.15.0/26
- 220.75.32.0/30
- 200.39.79.0/29
- 195.50.120.0/27
- 202.139.67.0/28
- Challenge 132.59.0.0/19
- Challenge 64.0.0.0/16
Answers
57
Answers
Dont Cheat Yourself!! Work them out before you
check your answers. Click the back button if
youre not done. Otherwise, click anywhere else
in the screen to see the answers.
Back
58
Routing Basics
- Path Determination Packet Switching
Network
Table of Contents
59
A Routers Functions
- A router is responsible for determining the
packets path and switching the packet out the
correct port. - A router does this in five steps
- De-encapsulates the packet
- Performs the ANDing operation
- Looks for entry in routing table
- Re-encapsulates packet into a frame
- Switches the packet out the correct interface
60
Routed v. Routing Protocols
- What is a routed protocol?
- Routed protocols are protocols that enable data
to be transmitted across a collection of networks
or internetworks using a hierarchical addressing
scheme. - Examples include IP, IPX and AppleTalk.
- A routable protocol provides both a network and
node number to each device on the network.
Routers AND the address to discover the network
portion of the address. - An example of a protocol that is not routable is
NetBEUI because it does not have a network/node
structure.
61
Routed v. Routing Protocols
- What is a routing protocol?
- A routing protocol is a protocol that determines
the path a routed protocol will follow to its
destination. - Routers use routing protocols to create a map of
the network. These maps allow path determination
and packet switching. Maps become part of the
routers routing table. - Examples of routing protocols include RIP, IGRP,
EIGRP, OSPF
62
Multi-protocol Routing
- Routers are capable of running multiple routing
protocols (RIP, IGRP, OSPF, etc.) as well as
running multiple routed protocols (IP, IPX,
AppleTalk). - For a router to be able use different routing and
routing protocols, you must enable the protocols
using the appropriate commands.
63
Dynamic v. Static Routing
- Dynamic routing refers to the process of allowing
the router to determine the path to the
destination. - Routing protocols enable dynamic routing where
multiple paths to the same destination exist.
64
Dynamic v. Static Routing
- Static routing means that the network
administrator directly assigns the path router
are to take to the destination. - Static routing is most often used with stub
networks where only one path exists to the
destination.
65
Default Routes
- A default route is usually to a border or gateway
router that all routers on a network can send
packets to if they do not know the route for a
particular network.
66
Routing Protocol Classes
- Routing protocols can be divided into three
classes - Distancevector determines the route based on
the direction (vector) and distance to the
destination - Link-state opens the shortest path first to the
destination by recreating an exact topology of
the network in its routing table - Hybrid combines aspects of both
67
Convergence
- Convergence means that all routers share the same
information about the network. In other words,
each router knows its neighbor routers routing
table - Every time there is a topology change, routing
protocols update the routers until the network is
said to have converged again. - The time of convergence varies depending upon the
routing protocol being used.
68
Distance-vector Routing
- Each router receives a routing table periodically
from its directly connected neighboring routers. - For example, in the graphic, Router B receives
information from Router A. Router B adds a
distance-vector number (such as a number of
hops), and then passes this new routing table to
its other neighbor, Router C.
69
Link-state Routing
- Link-state protocols maintain complex databases
that summarize routes to the entire network. - Each time a new route is added or a route goes
down, each router receives a message and then
recalculates a spanning tree algorithm and
updates its topology database.
70
Comparing the Two
71
Hybrid Routing
- Ciscos proprietary routing protocol, EIGRP, is
considered a hybrid. - EIGRP uses distance-vector metrics. However, it
uses event-triggered topology changes instead of
periodic passing of routing tables.
72
Transport Layer
Transport
- A Quick Review
Table of Contents
73
Transport Layer Functions
- Synchronization of the connection
- Three-way handshake
- Flow Control
- Slow down, youre overloading my memory
buffer!! - Reliability Error Recovery
- Windowing How much data can I send before
getting an acknowledgement? - Retransmission of lost or unacknowledged segments
74
Transports Two Protocols
- TCP
- Transmission Control Protocol
- Connection-oriented
- Acknowledgment Retransmission of segments
- Windowing
- Applications
- File Transfer
- E-Commerce
- UDP
- User Datagram Protocol
- Connectionless
- No Acknowledgements
- Applications
- Routing Protocols
- Streaming Audio
- Gaming
- Video Conferencing