User Interface and System Security and Controls PowerPoint PPT Presentation
1 / 66
Title: User Interface and System Security and Controls
1
ITEC 2010 Systems Analysis and Design, I
LECTURE 11
User Interface and System Security and Controls
Prof. Peter Khaiter
2
Topics
- Inputs and Outputs
- User and System Interface
- User-Centered Design
- Metaphors for HCI
- Designing System Inputs
- Designing System Outputs
- Designing Integrity Controls
- Designing Security Controls
- Managing User Access
- Data Security
3
Identifying and Classifying Inputs and Outputs
- Identified by analyst when defining system scope
- Requirements model produced during analysis
- Event table includes trigger to each external
event - Triggers represent inputs
- Outputs are shown as responses to events
4
Traditional and OO Approaches to Inputs and
Outputs
- Traditional approach to inputs and outputs
- Shown as data flows on context diagram, data flow
diagram (DFD) fragments, and detailed DFDs - OO approach to inputs and outputs
- Defined by message entering or leaving system
- Documented in system sequence diagram (SSD)?
- Actors provide inputs for many use cases
- Use cases provide outputs to actors
5
User versus System Interface
- System interfaces I/O requiring minimal human
interaction - User interfaces
- I/O requiring human interaction
- User interface is everything end user comes into
contact with while using the system - To the user, the interface is the system
- Analyst designs system interfaces separate from
user interfaces - Requires different expertise and technology
6
Understanding the User Interface
- Physical aspects of the user interface
- Devices touched by user, manuals, documentation,
and forms - Perceptual aspects of the user interface
- Everything else user sees, hears, or touches such
as screen objects, menus, and buttons - Conceptual aspects of the user interface
- What user knows about system and logical function
of system
7
Aspects of the User Interface
8
User-Centered Design
- Focus early on the users and their work by
focusing on requirements - Usability - system is easy to learn and use
- Iterative development keeps focus on user
- Continually return to user requirements and
evaluate system after each iteration - Human-computer interaction (HCI)
- Study of end users and interaction with computers
- Human factors engineering (ergonomics)?
9
Metaphors for Human-Computer Interaction
- Direct manipulation metaphor
- User interacts with objects on display screen
- Document metaphor
- Computer is involved with browsing and entering
data in electronic documents - WWW, hypertext, and hypermedia
- Dialog metaphor
- Much like carrying on a conversation
10
Desktop Metaphor Based on Direct Manipulation
Shown on Display Screen
11
Document Metaphor Shown as Hypermedia in Web
Browsers
12
Dialog Metaphor Expresses the Messaging Concept
13
Guidelines for Designing User Interfaces
- Visibility
- All controls should be visible
- Provide immediate feedback to indicate control is
responding - Affordance
- Appearance of control should suggest its
functionality purpose for which it is used - System developers should use published interface
design standards and guidelines
14
Eight Golden Rules for Interactive Interface
Design
15
Documenting Dialog Designs
- Done simultaneously with other system activities
- Based on inputs and outputs requiring user
interaction - Used to define menu hierarchy
- Allows user to navigate to each dialog
- Provides overall system structure
- Storyboards, prototypes, and UML diagrams
16
Overall Menu Hierarchy DesignEach Use Case is
Listed Under a MenuUtilities, Preferences, and
Help Are Added
17
Dialogs and Storyboards
- Many methods exist for documenting dialogs
- Written descriptions following flow of activities
like in use case description - Narratives
- Sketches of screens
- Storyboarding showing sequence of sketches of
display screen during a dialog
18
Storyboard for the Downtown Videos Rent Videos
Dialog
19
Guidelines for Designing Windows and Browser
Forms
- Each dialog might require several windows forms
- Standard forms are widely available
- Windows Visual Basic, C, C, Java
- Browser HTML, VBScript, JavaScript, ASP, Java
servlets - Implementation
- Identify objectives of form and associated data
fields - Construct form with prototyping tools
20
Form Design Issues
- Form layout and formatting consistency
- Headings, labels, logos
- Font sizes, highlighting, colors
- Order of data-entry fields and buttons
- Data keying and data entry (use standard
controls)? - Text boxes, list boxes, combo boxes, and so on
- Navigation and support controls
- Help support tutorials, indexes,
context-sensitive
21
Design for RMO Phone-Order Dialog
- Steps in dialog models
- Record customer information
- Create new order
- Record transaction details
- Produce order confirmation
- Traditional approach use structure charts
- OO approach expand SSD to include forms
22
Required Forms for RMO
- Main menu
- Customer
- Item search
- Product detail
- Order summary
- Shipping and payment options
- Order confirmation
23
Design Concept for Sequential Approach to Create
New Order Dialog
24
Design Concept for Order-Centered Approach to
Create New Order Dialog
25
Prototype Main Menu Form for Order-Centered
Approach to Dialog
26
Order Summary and Product Detail Forms
27
Completed Order Summary and Shipping Payment Forms
28
Identifying System Interfaces
- System interfaces are broadly defined as inputs
or outputs with minimal or no human intervention - Inputs from other systems (messages, EDI)?
- Highly automated input devices such as scanners
- Inputs that are from data in external databases
- Outputs to external databases
- Outputs with minimal HCI
- Outputs to other systems
- Real-time connections (both input and output)?
29
Just for Fun!
http//www.informationaddicts.com
30
Full Range of Inputs and Outputs
31
Design of System Inputs
- Identify devices and mechanisms used to enter
input - High-level review of most up-to-date methods to
enter data - Identify all system inputs and develop list of
data content for each - Provide link between design of application
software and design of user and system interfaces - Determine controls and security necessary for
each system input
32
Input Devices and Mechanisms
- Capture data as close to original source as
possible - Use electronic devices and automatic entry
whenever possible - Avoid human involvement as much as possible
- Seek information in electronic form to avoid data
re-entry - Validate and correct information at entry point
33
Prevalent Input Devices to Avoid Human Data Entry
- Magnetic card strip readers
- Bar code readers
- Optical character recognition readers and
scanners - Radio-frequency identification tags
- Touch screens and devices
- Electronic pens and writing surfaces
- Digitizers, such as digital cameras and digital
audio devices
34
Defining the Details of System Inputs
- Ensure all data inputs are identified and
specified correctly - Can use traditional structured models
- Identify automation boundary
- Use DFD fragments
- Segment by program boundaries
- Examine structure charts
- Analyze each module and data couple
- List individual data fields
35
Automation Boundary on a System-Level DFD
36
Create New Order DFD with an Automation Boundary
37
List of Inputs for Customer Support System
38
Data Flows, Data Couples, and Data Elements
Making Up Inputs
39
Using Object-Oriented Models
- Identifying user and system inputs with OO
approach has same tasks as traditional approach - OO diagrams are used instead of DFDs and
structure charts - System sequence diagrams identify each incoming
message - Design class diagrams and sequence diagrams
identify and describe input parameters and verify
characteristics of inputs
40
Partial System Sequence Diagram for Payroll
System Use Cases
41
System Sequence Diagram for Create New Order
42
Input Messages and Data Parameters from RMO
System Sequence Diagram
43
Designing System Outputs
- Determine each type of output
- Make list of specific system outputs required
based on application design - Specify any necessary controls to protect
information provided in output - Design and prototype output layout
- Ad hoc reports designed as needed by user
44
Defining the Details of System Outputs
- Types of reports
- Printed reports
- Electronic displays
- Turnaround documents
- Can use traditional structured models to identify
outputs - Data flows crossing automation boundary
- Data couples and report data requirements on
structure chart
45
Table of System Outputs Based on Traditional
Structured Approach
46
Using Object-Oriented Models
- Outputs indicated by messages in sequence
diagrams - Originate from internal system objects
- Sent to external actors or another external
system - Output messages based on an individual object are
usually part of methods of that class object - To report on all objects within a class,
class-level method is used that works on entire
class
47
Table of System Outputs Based on OO Messages
48
Designing Integrity Controls
- Mechanisms and procedures built into a system to
safeguard it and information contained within - Integrity controls
- Built into application and database system to
safeguard information - Security controls
- Built into operating system and network
49
Objectives of Integrity Controls
- Ensure that only appropriate and correct business
transactions occur - Ensure that transactions are recorded and
processed correctly - Protect and safeguard assets of the organization
- Software
- Hardware
- Information
50
Points of Security and Integrity Controls
51
Input Integrity Controls
- Used with all input mechanisms
- Additional level of verification to help reduce
input errors - Common control techniques
- Field combination controls
- Value limit controls
- Completeness controls
- Data validation controls
52
Database Integrity Controls
- Access controls
- Data encryption
- Transaction controls
- Update controls
- Backup and recovery protection
53
Output Integrity Controls
- Ensure output arrives at proper destination and
is correct, accurate, complete, and current - Destination controls - output is channeled to
correct people - Completeness, accuracy, and correctness controls
- Appropriate information present in output
54
Integrity Controls to Prevent Fraud
- Three conditions are present in fraud cases
- Personal pressure, such as desire to maintain
extravagant lifestyle - Rationalizations, including I will repay this
money or I have this coming - Opportunity, such as unverified cash receipts
- Control of fraud requires both manual procedures
and computer integrity controls
55
Fraud Risks and Prevention Techniques
56
Designing Security Controls
- Security controls protect assets of organization
from all threats - External threats such as hackers, viruses, worms,
and message overload attacks - Security control objectives
- Maintain stable, functioning operating
environment for users and application systems (24
x 7)? - Protect information and transactions during
transmission outside organization (public
carriers)?
57
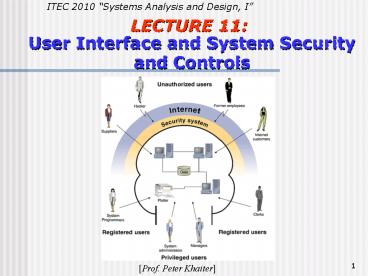
Security for Access to Systems
- Used to control access to any resource managed by
operating system or network - User categories
- Unauthorized user no authorization to access
- Registered user authorized to access system
- Privileged user authorized to administrate
system - Organized so that all resources can be accessed
with same unique ID/password combination
58
Users and Access Roles to Computer Systems
59
Managing User Access
- Most common technique is user ID / password
- Authorization Is user permitted to access?
- Access control list users with rights to access
- Authentication Is user who they claim to be?
- Smart card computer-readable plastic card with
embedded security information - Biometric devices keystroke patterns,
fingerprinting, retinal scans, voice
characteristics
60
Data Security
- Data and files themselves must be secure
- Encryption primary security method
- Altering data so unauthorized users cannot view
- Decryption
- Altering encrypted data back to its original
state - Symmetric key same key encrypts and decrypts
- Asymmetric key different key decrypts
- Public key public encrypts private decrypts
61
Symmetric Key Encryption
62
Asymmetric Key Encryption
63
Digital Signatures and Certificates
- Encryption of messages enables secure exchange of
information between two entities with appropriate
keys - Digital signature encrypts document with private
key to verify document author - Digital certificate is institutions name and
public key that is encrypted and certified by
third party - Certifying authority
- VeriSign or Equifax
64
Using a Digital Certificate
65
Secure Transactions
- Standard set of methods and protocols for
authentication, authorization, privacy, integrity - Secure Sockets Layer (SSL) renamed as Transport
Layer Security (TLS) protocol for secure
channel to send messages over Internet - IP Security (IPSec) newer standard for
transmitting Internet messages securely - Secure Hypertext Transport Protocol (HTTPS or
HTTP-S) standard for transmitting Web pages
securely (encryption, digital signing,
certificates)?
66
The End!
http//www.visualjokes.com