Background - PowerPoint PPT Presentation
Title:
Background
Description:
Background History TCSEC Issues non-standard inflexible not scalable The Global Information Grid (GIG) and the Common Criteria (CC) Common Criteria Sections I ... – PowerPoint PPT presentation
Number of Views:68
Avg rating:3.0/5.0
Title: Background
1
Background
2
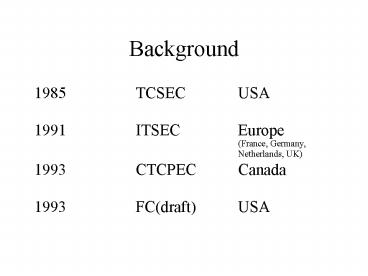
History
3
TCSEC Issues
- non-standard
- inflexible
- not scalable
4
The Global Information Grid (GIG) and the Common
Criteria (CC)
- Global Information Grid
- Clinger-Cohen Act of 1996 (reference (d)) and
- Title 10, U.S.C., Section 2223 (reference (a))
- All DoD and Intelligence Community Computers
- Information Assurance GPM
- 5.2.20. Consult the IA Technical Framework
(IATF) and published - Common Criteria (CC) Protection Profiles for
guidance regarding common - classes of network and system attacks,
interoperability and compatibility with - the defense-in-depth strategy, and IA solutions
that should be considered to - counter attacks.
- 5.2.21. Acquire IA solutions that have been
evaluated using the Common - Criteria Evaluation and Validation Scheme based
on the National Information - Assurance Program (NIAP) process.
- NIAP - Collaboration between NIST and NSA for
security evaluation
5
Common Criteria Sections
I. Introduction and General Model II. Security
Functional Requirements III. Security Assurance
Requirements
6
I. Introduction and General Model
- Defines general concepts and principals of IT
security evaluation. - Provides constructs for defining and selecting
security objectives - Provides guidelines for writing high-level
specifications
7
II. Security Functional Requirements
- Provides functional components
8
III. Security Assurance Requirements
- Provides assurance requirements
- Evaluation Criteria of PP and ST
- Provides evaluation levels with a predefined
scale (EALs)
9
Common Criteria
- I. Introduction and General Model
10
I. Introduction and General Model
Definitions- Target of Evaluation (TOE) An IT
product or system and its associated
administrator and user guidance
documentation that is the subject of an
evaluation. Protection Profile (PP) An
implementation-independent set of security
requirements for a category of TOEs that meet
specific consumer needs. Security Target (ST)
A set of security requirements and
specifications to be used as the basis for
evaluation of an identified TOE.
11
I. Introduction and General Model
- Protection Profiles
- Operating System
- Firewall
- Database
- Smart Card
- etc.
12
I. Introduction and General Model
- Security Targets
- NT 4.0
- Oracle 8
- Checkpoint-1
- Visa SmartCard
- etc.
13
(No Transcript)
14
(No Transcript)
15
Requirements Structure
- Class
- Family
- leveling-specifies if components are hierarchic
- Component
- dependencies-other components that are relied upon
16
Requirements Structure
CLASS_FAMILY.Component Class FIA-Identification
and authentication Family FIA_UID-User
Identification Component FIA_UID.1-Timing of
Identification
17
Common Criteria
- II. Security Functional Requirements
18
II. Security Functional Requirements
Hierarchy of Security Functional Requirements
19
II. Security Functional Requirements
- Security Functional Component
- Dependencies
- -Components rely on other components for
satisfaction - Operations
- -Iteration
- -Assignment
- FAU_ARP.1.1 The TSF shall take assignment
list of the least disruptive actions
upon detection of a potential
security violation. - -Selection
- FAU_GEN.1.1 The TSF shall be able to
generate an audit record of the following
auditable events - a) Start-up and shutdown of the
audit functions - b) All auditable events for the
selection minimum, basic, detailed, not - specified level of audit
- -Refinement
20
II. Security Functional Requirements
Security Functional Classes
Class FAU FCO FCS FDP FIA FMT FPR FPT FRU FTA FTP
Name Audit Communications Cryptographic
Support User Data Protection Identification
Authentication Security Management Privacy Protect
ion of TOE Security Functions Resource
Utilization TOE Access Trusted Path / Channels
21
Common Criteria
- III. Security Assurance Requirements
22
III. Security Assurance Requirements
Definitions- Package A reusable set of either
functional or assurance components (e.g. an
EAL), combined together to satisfy a set of
identified security objectives. Evaluation
Assurance Level (EAL) A package
consisting of assurance components from Part 3
that represents a point on the CC predefined
assurance scale.
23
III. Security Assurance Requirements
Hierarchy of Security Assurance Requirements
24
III. Security Assurance Requirements
Security Assurance Classes
Class ACM ADO ADV AGD ALC ATE AVA APE ASE AMA
Name Configuration Management Delivery
Operation Development Guidance Documents Life
Cycle Support Tests Vulnerability
Assessment Protection Profile Evaluation Security
Target Evaluation Maintenance of Assurance
25
III. Security Assurance Requirements
Evaluation Assurance Levels
26
(No Transcript)
27
Current Certified Protection Profiles
- C2 Controlled Access Protection Profile (Version
1.d) - B1Labeled Security Protection Profile (Version
1.b) - Traffic Filter Firewall Protection Profile for
Low Risk Environments (Version 1.d)
28
Controlled Access Protection Profile (CAPP)
- Version 1.d
- Written by NSA
- Designed to replace C2
29
C2 vs CAPP
30
New Items in CAPP
- 5.1 Security Audit-lists 19 auditable events
- All modifications to the values of security
attributes - Actions taken due to audit storage failure
- 5.3.2 Strength of Authentication Data
- Single guess has less than 1/1,000,000 chance
- Multiple attempts in one minute have less than
1/100,000 chance - 5.4 Security Management-specifies requirements
and roles. - 6.2 Delivery and Operation
31
Labeled Security Protection Profile(LSPP)
- Version 1.b
- Developed by NSA
- Designed to replace B1
32
B1 vs LSPP
33
New Items in LSPP
- 5.1 Security Audit-lists 19 auditable events
- All attempts to import user data, including any
- security attributes
- Actions taken due to audit storage failure
- 5.3.2 Strength of Authentication Data
- Single guess has less than 1/1,000,000 chance
- Multiple attempts in one minute have less than
1/100,000 chance - 5.4 Security Management-specifies requirements
and roles. - 6.2 Delivery and Operation
34
ISO/IEC PDTR 15446
- Expands on PPs and STs
- PPs and STs for composite TOEs
- Functional and Assurance Packages
- Generic and Worked Examples
35
Websites of Interest
Common Criteria NIST- csrc.ncsl.nist.gov/cc CC
Toolbox- niap.nist.gov/tools/cctool.html Others GI
G- cno-n6.hq.navy.mil/files.htm NIAP-
niap.nist.gov