Talk Outline - PowerPoint PPT Presentation
1 / 110
Title:
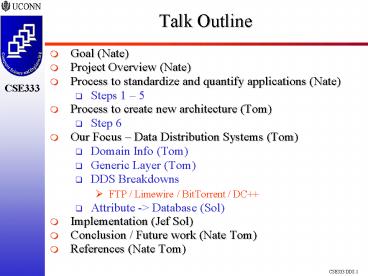
Talk Outline
Description:
Talk Outline Goal (Nate) Project Overview (Nate) Process to standardize and quantify applications (Nate) Steps 1 5 Process to create new architecture (Tom) – PowerPoint PPT presentation
Number of Views:238
Avg rating:3.0/5.0
Title: Talk Outline
1
Talk Outline
- Goal (Nate)
- Project Overview (Nate)
- Process to standardize and quantify applications
(Nate) - Steps 1 5
- Process to create new architecture (Tom)
- Step 6
- Our Focus Data Distribution Systems (Tom)
- Domain Info (Tom)
- Generic Layer (Tom)
- DDS Breakdowns
- FTP / Limewire / BitTorrent / DC
- Attribute -gt Database (Sol)
- Implementation (Jef Sol)
- Conclusion / Future work (Nate Tom)
- References (Nate Tom)
2
A System for Creating Specialized DDS
Architectures
Research and Work By Tom Puzak Nathan
Viniconis Solomon Berhe Jeffrey Peck
Project web site http//www.revrick.net/CSE333/P
rojectTimeline.htm
3
A System for Creating Specialized DDS
Architectures - Outline
- Goal
- Responsibilities
- Project Overview
- Phase 1 Break down existing applications within
the domain. - Steps 1 5
- Phase 2 Process to create new architecture
- Step 6
- Our Focus Data Distribution Systems
- Domain Info
- Generic Layer
- DDS Breakdowns
- FTP / Limewire / BitTorrent / DC
- Attribute -gt Database
- Implementation
- Conclusion / Future work
- References
4
Goal
- Outline a process of generating an architecture
of an application derived from a breakdown of
similar applications. Show it can work. - Create a generic procedure that can be extended
to a variety of domains within Software
Engineering. - Test our procedure with an implementation
focusing on the DDS domain.
5
A System for Creating Specialized DDS
Architectures - Outline
- Goal
- Responsibilities
- Project Overview
- Phase 1 Break down existing applications within
the domain. - Steps 1 5
- Phase 2 Process to create new architecture
- Step 6
- Our Focus Data Distribution Systems
- Domain Info
- Generic Layer
- DDS Breakdowns
- FTP / Limewire / BitTorrent / DC
- Attribute -gt Database
- Implementation
- Conclusion / Future work
- References
6
Responsibilities
- Universal Procedures to
- strip applications down to their generic models.
- analyze and extend the generic models to a
particular application. - tag and store the attributes in an organized way
- create a new application using a sum of parts
method - Nate
- Webpage Maintenance
- http//www.revrick.net/CSE333/ProjectTimeline.htm
- BitTorrent Analysis
- Tom
- FTP Analysis
- Solomon
- Limewire Analysis
- Implementation
- http//www.berhe.info/cse333/index.php
- Jeff
- DC Analysis
7
A System for Creating Specialized DDS
Architectures - Outline
- Goal
- Responsibilities
- Project Overview
- Phase 1 Break down existing applications within
the domain. - Steps 1 5
- Phase 2 Process to create new architecture
- Step 6
- Our Focus Data Distribution Systems
- Domain Info
- Generic Layer
- DDS Breakdowns
- FTP / LimeWire / BitTorrent / DC
- Attribute -gt Database
- Implementation
- Conclusion / Future work
- References
8
Project Overview
- Goal Outline a process of generating an
architecture of an application derived from a
breakdown of similar applications. - Significant Changes
- Created generic abstraction from our DDS focus.
- Generic Outline
- Phase 1 Break down existing applications within
the domain. - Phase 2 Creation of a new architecture.
- Extending to the DDS domain
- Implementation
- http//www.berhe.info/cse333/index.php
- Conclusion / Future work
9
Project Overview-Phase 1
Knowledge Database
Application Domain
Analysis, Tagging, and Organizing
Initial
x
Application Subset
Generic Models Minimal Subset
Standardized Components
10
Project Overview - Phase 2
Generated Architecture
Users
Completed Architecture
Main Components
Knowledge Database
Attribute Sets
11
A System for Creating Specialized DDS
Architectures - Outline
- Goal
- Responsibilities
- Project Overview
- Phase 1 Break down existing applications within
the domain. - Steps 1 5
- Phase 2 Process to create new architecture
- Step 6
- Our Focus Data Distribution Systems
- Domain Info
- Generic Layer
- DDS Breakdowns
- FTP / Limewire / BitTorrent / DC
- Attribute -gt Database
- Implementation
- Conclusion / Future work
- References
12
Phase 1 Overview
- Phase 1 Break down existing applications within
the domain. - Find suitable subset of the domain
- Define the domain using Generic Models (GM)
- Break down each application and
- Find shared major components
- Create conceptual structural diagrams
- Create unified view
- Create generic layer
- Organize and tag the added functionality
- Store the result in a Knowledge Database
- Allow additional applications to be added to the
Knowledge Database. - Extensions Behavioral models, GM maintenance.
13
Phase 1 Finding a suitable subset
- Choose applications within
- the domain that
- Maximize percentage of
- functionality coverage
- Choose applications with
- Best Open source
- Worse Proprietary software but heavily
researched - Worst Small, proprietary, non-analyzed
- The end result can only be created from the
subset of applications chosen - so choose wisely!
- Create UML 2.0 Class and Use Case diagrams for
each application.
14
Phase 1 Define the domain using Generic Models
- Step 1 Find shared major components
- Step 2 Break the components into disjoint
entities
Comp1
Comp2
App1
AppN1
Comp3
CompN2
15
Phase 1 Define the domain using Generic Models
- Step 3 Create unified view of each component
- Combine UML Class Diagrams together into a
superset. - Merge classes that overlap between 2 apps
- Create relationships between apps
- Step 4 Identify or abstracting out generic
classes - Identifying generic classes
- A class exists that is exactly the same in every
app - Abstracting out generic classes
- Classes exist that contain similar functionality
in every application - Create a new class that all applications can
inherit
16
Phase 1 Organize and tag the added functionality
- Each application inherits from the GM Class
Diagrams. - The Generic Classes are tailored to a more
specific instance when inherited from. - Defining the Attributes.
- Augmenting it to store additional information
- Addition of methods to increase scope of
functionality - Store the Attributes in a database.
Application Class
Generic Class
17
Phase 1 Extensions
- Other aspects can be modeled into a generic
layer. - Behavioral Models
- Storyboard / Activity / Work-Flow
- Security Models
- Reuse Models
- Multi-layered inheritance tagging
- Augment attributes with extracted code segments
2
1
18
A System for Creating Specialized DDS
Architectures - Outline
- Goal
- Responsibilities
- Project Overview
- Phase 1 Break down existing applications within
the domain. - Steps 1 5
- Phase 2 Process to create new architecture
- Step 6
- Our Focus Data Distribution Systems
- Domain Info
- Generic Layer
- DDS Breakdowns
- FTP / Limewire / BitTorrent / DC
- Attribute -gt Database
- Implementation Process
- Conclusion / Future work
- References
19
Phase 2 Process to create new architecture
- 1) User selects a generic component to model
- Generic components defined in Phase 1
- 2) User selects desired attributes that
correspond to the chosen generic component - 3) Steps 1 and 2 are repeated for each component
in the general architecture - A model of a new architecture is produced
- Architectural components are chosen based on
desired attributes - New architecture is based on preexisting
architectures
20
A System for Creating Specialized DDS
Architectures - Outline
- Goal
- Responsibilities
- Project Overview
- Phase 1 Break down existing applications within
the domain. - Steps 1 5
- Phase 2 Process to create new architecture
- Step 6
- Our Focus Data Distribution Systems
- Domain Info
- Generic Layer
- DDS Breakdowns
- FTP / LimeWire / BitTorrent / DC
- Attribute -gt Database
- Implementation
- Conclusion / Future work
- References
21
Focus Domain Information
- DDSs come in many forms
- Client-Server
- Peer to Peer
- Centralized
- Decentralized
- They provide the same basic service
- Therefore they have similar components
- The functionality of these components may differ,
but their basic goals are the same
22
Focus Generic Layer Basic Components
- Regardless of implementation, all DDSs must
provide these services - Network Communication
- Search or content location capabilities
- Authentication
- User Interaction
- Security
- Data Handling
23
Main Component Focus
- We chose to focus our study on two main
components - Network Communication
- Search
- They are related
- Probably need to search across a network
- Must create a highly abstract view of the
functionality in order to create a successful
model - Our in dept analysis corresponds to these domains
24
Generic Network Communication Classes
- Classes common to all DDS network communication
components - Network Entity
- Connection
- Generic Listener
- Data Handler
- Control Message
25
Generic Network Communication
26
Generic Search Classes
- Search
- The highest level description of a search
- Result
- A high level result class
27
Generic Search
28
DDS Breakdowns FTP
- FTP Basics
- Screen-shots
- Functionality
- Modes
- FTP Structure
- The Diagram
- Network Communication Component
- UML and attributes
- Search Component
- UML and attributes
29
Console FTP
30
GUI FTP
31
FTP Basics
- Classical client server model
- Client initiates connection with the server
- Server responds to client's requests
- Two separate connections for every FTP session
- Control messages
- Data transfer connection (not always present)
- Control messages are handled by the Telnet
protocol (RFC 854)
32
FTP Modes
- Active this entity initiates the data
connection - Passive the entity that waits for a data
connection - By default the FTP client is passive and the
server is active - The client can switch to active and instruct the
server to be passive - Common practice because of firewalls
- Also modes for file transfer details
- Block size, etc..
33
FTP Structure
- The Protocol Interpreter (PI) is responsible
for the control messages, and dictates the
behavior of the DTP - The Data Transfer Process (DTP) handles
transferring data, and interfaces with the file
system - Telnet client and server
34
FTP The Diagram
Taken from RFC 959
35
FTP Network Communication Use Case
36
FTP Network Communication Class Diagram
37
FTP Network Communication Attributes
- FTP Entity Only two connections allowed
- FTP Control Connection Utilizes FTP specific
messages - FTP Control Listener Waits on FTP control port
for FTP control connections - FTP Data Listener Waits of FTP data port for
FTP data connections - FTP Data Handler Considers the FTP mode when
sending/receiving files
38
FTP Network Communication Attributes
39
FTP Search Use Case
40
FTP Search Class Diagram
41
FTP Search Attributes
- FTP Search Considers FTP Specific search
constraints - Based on Telnet commands
- FTP Result FTP formatted result strings
42
DDS Breakdowns LimeWire
- Limewire Basics
- Virtual Network
- Use Cases
- Network Communication
- Use Case
- Class Diagram
- Query
- Screenshot
- Class Diagram
43
Limewire / Basics
Distributed File Sharing Application
Freeware and Open API
Based on Gnutella Network (GNode)
Runs on all common Operating Systems
44
Limewires Virtual Network
Virtual Gnutella Network
New Servant How does he become a GNode ?_
Virtual Mapping
Internet
45
Limewire/Network
Ping()
Ping()
Ping()
Pong()
Ping()
46
Limewire/ UseCase
47
Limewire/ UseCase
48
Limewire Search
49
Limewire / Search
QueryRequest SearchString MinSpeed TTL1
QueryReply IPAddress Port
QueryRequest SearchString MinSpeed TTL0
QueryReply IPAddress Port
QueryRequest SearchString MinSpeed TTL2
QueryReply IPAddress Port
PushRequest Send over Internet
50
Limewire/ Screenshot
51
Limewire/ UML Diagramm
Generic Classes
Application Classes
52
Limewire / Attributes
- Generic Search
- Limewire Specific SearchString
- MinSpeed
- Generic ControlMessage
- Limewire Specific Message
- Ping
- Pong
- QueryRequest
- QueryReply
- PushQueryRequest
53
DDS Breakdowns BitTorrent
- Overview
- BitTorrent Basics
- How it works
- Run-through of the application
- Analysis
- Derivation of major entities
- Search
- Use Case
- Class Diagram
- Attributes
- Network Communication
- Use Case
- Class Diagram
- Attributes
- Adding it to the Knowledge Domain
54
BitTorrent Overview
HOW?
HOW?
HOW?
HOW?
does it work?
can it be modeled?
55
BitTorrent Overview
- The BitTorrent Protocol -Background
- Bram Cohen began designing the protocol in 2001.
- First implementations available mid 2002.
- The BitTorrent Protocol
- Standardizes file transactions among many
simultaneous peers. - Utilizes a tit-for-tat exchange technique.
- BitTorrent Basics
- How it works.
- Outline of the BitTorrent Search and Download
process. - BitTorrent Analysis
- Use Cases, Class Diagrams, and Attribute
Selection. - Storing the standardized data in the Knowledge
Database
56
BitTorrent Basics
- User opens program to allow BitTorrent
connections.
User
Is The
- User opens their favourite web browser and heads
to a Torrent Database.
Time
57
BitTorrent Basics
- User navigates the Database Search Application
(DSA).
- A) User selects a torrent. or-
- B) User enters a search ?
User
Time
Please do not sue me.
58
BitTorrent Basics
- Generic keyword search.
- Keyword(s) entered, resulting Torrents returned.
- Torrent is selected
User
Time
?
59
BitTorrent Basics
- Torrent meta-data is displayed.
User
The Tracker
Time
?
60
BitTorrent Basics
User
- Active Torrent
- Info
?
Time
- Cancel
- Queued Torrent
61
BitTorrent Basics
- Torrent information displayed
User
Peer1
Peer2
Peer3
Client
.......
.....
Time
Tracker
Tracker DB
62
BitTorrent Analysis
- Show derivation of major entities
- Search
- Use Case
- Generic Overview
- Class Diagram
- Attributes
- Network Communication
- Use Case
- Generic Overview
- Class Diagram
- Attributes
- Adding the analysis Knowledge Database
63
BitTorrent AnalysisDeriving the Entities
Connects too and Finds a Torrent through
Downloads meta-info file, aka .torrent
Starts
Add Torrent
Has a
Send Peer Information
Connects over http, Register user
Repeat until cancelled, Request Peers
64
BitTorrent AnalysisSearch - Use Case
65
BitTorrent AnalysisSearch - Generic Overview
66
BitTorrent AnalysisSearch - Class Diagram
- The class diagram has been derived from the
generic layer.
- The Generic Layer
- The classes that directly inherit from the
generic layer.
67
BitTorrent Analysis Attribute Selection
- Tagging of the inheritance from generic to
application layer - Search
- Generic Search ? BitTorrentSearch
- Database Keyword Search
- Generic Result ? Match
- Contains Connection Information
- Contains File Hash
68
BitTorrent AnalysisNetwork Communication Use
Case
http//www.revrick.net/CSE333/NC-Use.JPG
Over HTTP or HTTPS
Over TCP
69
BitTorrent AnalysisNetwork Communication -
Generic Overview
70
BitTorrent AnalysisNetwork Communication - Class
Diagram
- The class diagram has been derived from the
generic layer.
- The Generic Layer
- The classes that directly inherit from the
generic layer.
71
BitTorrent Analysis Attribute Selection
- Tagging of the inheritance from generic to
application layer - Network Communication
- NetworkEntity ? Peer
- Contains List of Connections to other Peers
- NetworkEntity ? Tracker
- HTTP Connection
- Manages a Network of Communicating Peers
- Connection ? BitTorrent Data Connection
- Binary Connection
- Connection ? BitTorrent Control Connection
- String Connection
- GenericListener ? Peer Control Listener
- Listen for / Create Peer String Connections
- GenericListener ? Peer Data Listener
- Listen for / Create Peer Data Connections
- DataHandler ? BitTDataHandler
- Define Packet Size
- Verify with SHA1 Hash
- ControlMessage ? BitTorrentMessage
72
BitTorrent AnalysisAdding the analysis Knowledge
Database
- Each extension from the generic classes to
another class is recorded in the database.
73
DDS Breakdowns DC
- What does it do?
- The Client
- Features
- Search
- Use Case
- Class Diagram
- Attributes
- NC
- Use Case
- Class Diagram
- Attributes
74
Direct Connect What does it do?
- There are Users (Clients) and there are Hubs.
75
Direct Connect What does it do?
- The Client
- Each Client has a filelist, which is
essentially an XML file that tells what files
that user has to share, and where they can be
found. - A Client can connect to a Hub, logging in with a
unique user ID, to access a list of other
connected Users, view any other User's filelist,
obtain information about other users, and search
the Hub. - When the Client finds a particular file, he can
establish a direct connection with that user and
start the file transfer. - If the Client logs in as Op it will have
special privileges to control the Hub.
76
Direct Connect ClientSearch Results Screen Shot
77
Direct Connect What does it do?
- The Hub
- The Hub maintains a list of all connected Users
(the Clients who are logged into the Hub). - The Hub has the ability to grant access to Users
based on Username and Password, as well as the
size of their filelist. - A Hub will have the responsibility of obtaining
search results from the list of connected Users,
for any search request from a particular Client. - Further, a Hub should be able to provide the
necessary information for any Client to be able
to connect to any connected User to initiate a
file transfer.
78
Direct Connect Protocol - Features
- Centralized - The Direct Connect Protocol is a
Peer-to-Peer protocol that is unlike Gnuetella or
BitTorrent in that it uses a central server the
Hub. - Security Direct Connect Hubs are able to
monitor which Users can connect based on the size
of their filelist. Further, special access can
be granted to Op Users. - Privateness Anyone with enough bandwidth and
hardware can set up a DC Hub, which as long as it
is not publicized can potentially remain unknown. - Due to being Centralized
- Basic File Transfer Does not deal with segments
of files.
79
DC
- DC is one of the many clients available that
uses the DC Network. - It is Open Source as most of the other Direct
Connect Clients. - There is no official Direct Connect Protocol
Standard, however DC has become the form of the
protocol that has been accepted.
80
DC - Protocol
81
DC - Search Use Case
82
DC - Search Class Diagram
83
DC - Search Attribute Selection
- Search ? DC_Client
- Send Search String to a Specific DC Hub, with
DC-specific parameters - Result ? DC_SearchResults
- List Files With File Paths on Connected Users, on
specific Hubs
84
DC - Network CommunicationUse Case
85
DC - Network CommunicationClass Diagram
86
DC - Network CommunicationAttribute Selection
- NetworkEntity ? DC_User
- Holds DC-specific user information
- Maintains a requestable filelist
- NetworkEntity ? DC_Hub
- Holds DC-specific hub information
- Maintains a list of connected Users
- Has security control
87
DC - Network CommunicationAttribute Selection
- Connection ? DC_Connection
- DC-specific connection protocol
- Handles DC Client-Hub and Client-Client Handshake
88
DC - Network CommunicationAttribute Selection
- DataHandler ? DC_Data Handler
- Send / Receive User File
89
DC - Network CommunicationAttribute Selection
- ControlMessage ? DC_Message
- Interpret DC-specific Client-Hub NMDC or ADC
commands - Interpret DC-specific Client-Client command
- GenericListener ? DC_ConnectionListnener
- Listen for incoming DC Connections for Client or
Hub
90
DC - Network CommunicationAttribute Selection
- NetworkEntity ? DC_User
- Holds DC-specific user information
- Maintains a requestable filelist
- NetworkEntity ? DC_Hub
- Holds DC-specific hub information
- Maintains a list of connected Users
- Has security control
- Connection ? DC_Connection
- DC-specific connection protocol
- Handles DC Client-Hub and Client-Client Handshake
- DataHandler ? DC_Data Handler
- Send / Receive User File
- ControlMessage ? DC_Message
- Interpret DC-specific Client-Hub NMDC or ADC
commands - Interpret DC-specific Client-Client command
- GenericListener ? DC_ConnectionListnener
- Listen for incoming DC Connections for Client or
Hub
91
Database / Structure
- Storing the attributes
- Attribute
- ATTRIBUT_ID
- ATTRIBUT_NAME
- CLASS_NAME
- GClass
- GCLASS_ID
- GCLASS_NAME
- DDS
- DDS_ID
- DDS_NAME
- USER_DDS
- USER_ID
- GCLASS_ID
- DDS_ID
- ATTRIBUT_ID
- DDS_GCLASS_ATTR
- GCLASS_ID
- DDS_ID
- ATTRIBUT_ID
92
A System for Creating Specialized DDS
Architectures - Outline
- Goal
- Responsibilities
- Project Overview
- Phase 1 Break down existing applications within
the domain. - Steps 1 5
- Phase 2 Process to create new architecture
- Step 6
- Our Focus Data Distribution Systems
- Domain Info
- Generic Layer
- DDS Breakdowns
- FTP / Limewire / BitTorrent / DC
- Attribute -gt Database
- Implementation
- Conclusion / Future work
- References
93
Implementation Specification
- Input
- Generic Classes
- DDS
- Attributes
- Output
- An XML File which contains a general
specification of the customized DDS. - Statistics regarding to preferred DDS
94
Implementation / Use Case
95
Implementation / Activity Diagram
96
Implementation / Activity Diagram
97
Implementation / Activity Diagram
98
Implementation / Technology
- Languages
- PHP
- HTML
- CSS
- Database
- MySQL
99
Implementation / Architecture
Model
Controller
View
100
Implementation Process
101
Implementation / Screen Shot Frontend
102
Implementation / Screen Shot Frontend
103
Implementation / XML Output
104
Implementation / Screen Shot Backend
105
A System for Creating Specialized DDS
Architectures - Outline
- Goal
- Responsibilities
- Project Overview
- Phase 1 Break down existing applications within
the domain. - Steps 1 5
- Phase 2 Process to create new architecture
- Step 6
- Our Focus Data Distribution Systems
- Domain Info
- Generic Layer
- DDS Breakdowns
- FTP / Limewire / BitTorrent / DC
- Attribute -gt Database
- Implementation
- Conclusion / Future work
- References
106
Conclusion
- What was accomplished --
- Created a method for defining an architecture in
terms of UML 2.0 Use Case and Class diagrams - Modeling granularity must stay consistent
- Outlined and tested a procedure to create a
generic abstraction from the diagrams - The generic layer has to portray correct and
consistent information throughout the domain - The generic layer defines the domain in terms of
conceptual class interactions. - Researched the detailed workings of applications
within the DDS domain. - Created a program outlining the methodologies of
this work.
107
Future Work
- Extraction of Generic Architecture from
application source. - Behavioral Extension
- Code generation
- For Implementation
- XML Output for UML Generator
- More User Friendly Interface
- PHP Session ID
- Security Mechanism
- Control over the DDSs to select
- More DDS, Functionalities and Attributes
108
A System for Creating Specialized DDS
Architectures - Outline
- Goal
- Responsibilities
- Project Overview
- Phase 1 Break down existing applications within
the domain. - Steps 1 5
- Phase 2 Process to create new architecture
- Step 6
- Our Focus Data Distribution Systems
- Domain Info
- Generic Layer
- DDS Breakdowns
- FTP / Limewire / BitTorrent / DC
- Attribute -gt Database
- Implementation
- Conclusion / Future work
- References
109
References
- Creating a Generic Model
- Combining Clustering with Pattern Matching for
Architecture Recovery of OO Systems Bauer et
al., FZI Forschungszentrum Informatik. Karlsruhe,
Germany. - Recovering UML Diagrams from Java Code using
Patterns Niere et al., University of Paderborn
WarburgerstraBe 100, Germany. - Generic Representation of Military Organization
and Military Behaviour UML and Bayesian
Networks Suzic. Swedish Defence Research Agency
(FOI) Stockholm, Sweden - Generic Modeling using UML extensions for
variability ClauB, Matthias et al., Software
Engineering Group, Dresden 2001. - BitTorrent
- Eger, K., Killat U., "Scalability of the
BitTorrent P2P Application," 5.Wurzburger
Workshop, Hamburg University of Technology
18.-19. 2005 - J.A. Pouwelse, P. Garbacki, D.H.J. Epema, H.J.
Sips. "The BitTorrent P2P File-Sharing System
Measurements and Analysis," Delft University of - http//www.bittorrent.com/protocol.html - The
BitTorrent Protocol - Final Fantasy I, NES User Image
110
References
- DC
- http//www.dcpp.net/
- http//sourceforge.net/projects/dcplusplus/
- http//www.b.ali.btinternet.co.uk/DCPlusPlus/
- http//en.wikipedia.org/wiki/Direct_Connect_networ
k/ - Limewire
- www.limewire.org
- http//www9.limewire.com/developer/gnutella_protoc
ol_0.4.pdf - http//rfc-gnutella.sourceforge.net/
- FTP
- J. Postel, J. Reynolds. "RFC 854 Telnet Protocol
Specification", Network Working Group, ISI May
1983. - J. Postel, J Reynolds. "RFC 959 File Transfer
Protocol (FTP)", Network Working Group, ISI
October 1985. - "Active FTP vs. Passive FTP, a Definitive
Explanation" http//slacksite.com/other/ftp.html.