Network Visibility PowerPoint PPT Presentations
All Time
Recommended
Niagara Networks believes that informing and educating our clients will instil in them the knowledge required to improve network monitoring and security capabilities for overall enhanced network visibility, and at the same time give them with a comprehensive understanding of the various concepts and aspects associated with network visibility. This presentation is intended to provide you with invaluable educational content in the form of blogs so that you can achieve maximum visibility for your network. Get ready to delve into topics on network monitoring tools, security for multi-site networks, network bypass switches, and more.
| PowerPoint PPT presentation | free to download
Niagara Networks believes that informing and educating our clients will instil in them the knowledge required to improve network monitoring and security capabilities for overall enhanced network visibility, and at the same time give them with a comprehensive understanding of the various concepts and aspects associated with network visibility. This presentation is intended to provide you with invaluable educational content in the form of blogs so that you can achieve maximum visibility for your network. Get ready to delve into topics on network monitoring tools, security for multi-site networks, network bypass switches, and more.
| PowerPoint PPT presentation | free to download
Niagara Networks believes that informing and educating our clients will instil in them the knowledge required to improve network monitoring and security capabilities for overall enhanced network visibility, and at the same time give them with a comprehensive understanding of the various concepts and aspects associated with network visibility. This presentation is intended to provide you with invaluable educational content in the form of blogs so that you can achieve maximum visibility for your network. Get ready to delve into topics on network monitoring tools, security for multi-site networks, network bypass switches, and more.
| PowerPoint PPT presentation | free to download
Network+ Guide to Networks 5th Edition Chapter 1 ... 5th Edition * Transmission Media Figure 1-8 Examples of network transmission media Joe uses a computer at Kinko ...
| PowerPoint PPT presentation | free to download
Distinguish between client/server and peer-to-peer networks ... BitTorrent software. Network Guide to Networks, 5th Edition. 10. Client/Server Networks ...
| PowerPoint PPT presentation | free to view
Network+ Guide to Networks 5th Edition Chapter 1 An Introduction to Networking Transmission Media Figure 1-8 Examples of network transmission media Notes on Network+ ...
| PowerPoint PPT presentation | free to download
Network-Wide Traffic Models for Managing IP Networks Jennifer Rexford Internet and Networking Systems AT&T Labs - Research; Florham Park, NJ http://www.research.att ...
| PowerPoint PPT presentation | free to download
Managed Network Services and Network Outsourcing Market research report analyses the market potential in terms of segments such as Managed Network Services by components, by types of services offered, by organization size and by business verticals across five major geographies, with projected forecasts of market size and expected revenues.
| PowerPoint PPT presentation | free to download
Managed Network Services and Network Outsourcing Market research report analyses the market potential in terms of segments such as Managed Network Services by components, by types of services offered, by organization size and by business verticals across five major geographies, with projected forecasts of market size and expected revenues.
| PowerPoint PPT presentation | free to download
Daniel King, Old Dog Consulting. Agenda. Commercial Objectives. Overlay ... Maybe 'packet optical' is the wrong name! Introducing Integrated Optical Networks ...
| PowerPoint PPT presentation | free to download
Can two private networks with same IP address space be connected together by NAT ... a SYN packet using its internal IP address, 10.0.0.3. PROTO. SADDR. DADDR ...
| PowerPoint PPT presentation | free to view
Definition of Recovery, Protection and Restoration. Causes of client connection unavailability ... availability against the cost of additional network resources ...
| PowerPoint PPT presentation | free to download
But network analysis implies a new perspective for understanding ... Family & Social Network, 1957 ... Perspectives on Social Network Research,1979 ...
| PowerPoint PPT presentation | free to view
Foundations Ubiquitous Sensor Networks Self-Organized Network - Routing and Forwarding David E. Culler University of California, Berkeley Embedded IP Architecture ...
| PowerPoint PPT presentation | free to download
[229 Pages Report] Managed Network Services and Network Outsourcing Market research report analyses the market potential in terms of segments such as Managed Network Services by components, by types of services offered, by organization size and by business verticals across five major geographies, with projected forecasts of market size and expected revenues.
| PowerPoint PPT presentation | free to download
Rubee Smart Tags. 2mm - 0.78mm thick. Visible 9. The RuBee Tags. Tags are Simple. Chip ... Rubee P1902.1 Summary. Long Battery Life. Long Range. Volumetric ...
| PowerPoint PPT presentation | free to view
Aim: knowledge about concepts in network theory, and being able to apply them, ... units (e.g. individuals) of the social system (e.g. project group) beforehand ...
| PowerPoint PPT presentation | free to view
1888 Press Release -Dynamite Agent delivers best-in-class network visibility and cybersecurity alerts with Zeek and Suricata via AWS VPC Traffic Mirroring.
| PowerPoint PPT presentation | free to download
The methods of social networks assume that there are no theoretical limitations ... A social network arises when all actors can, theoretically, have ties to ...
| PowerPoint PPT presentation | free to view
Network management is the process of administering and managing computer networks. Various services provided by this discipline include fault analysis, performance management, provisioning of networks, maintaining the quality of service, and so on.
| PowerPoint PPT presentation | free to download
PowerPoint Presentation ... Neural Networks
| PowerPoint PPT presentation | free to download
The name and the address of hosts and network devices. The opened services. ... Before this paper: ... Denial of Service (DDoS) Network Invasion Network ...
| PowerPoint PPT presentation | free to download
UNIT 3 NETWORK LAYER Network Layer It is responsible for end to end (source to destination) packet delivery, whereas the data link layer is responsible for node to ...
| PowerPoint PPT presentation | free to download
Network monitoring gives you the visibility you need to stay one step ahead of potential issues. By showing live network performance data in an easy-to-read interface, network monitoring software helps you identify outages that could cause bottlenecks.
| PowerPoint PPT presentation | free to download
Why Satellite Networks ? Wide geographical area coverage From kbps to Gbps communication everywhere Faster deployment than terrestrial infrastructures Bypass clogged ...
| PowerPoint PPT presentation | free to view
C E N T R F O R I N T E G R A T I V E E B I O I N F O R M A T I C S V U Intracellular Networks (2) Intracellular Network Behaviour Slides on: http://www.ibi.vu.nl ...
| PowerPoint PPT presentation | free to download
Network Computing The Web Revolution * * * * * * * * * * * * * * * * * * * Communication Modes People-to-people People-to-machine People and machine-to-machine ...
| PowerPoint PPT presentation | free to view
Why Satellite Networks ? Wide geographical area coverage From kbps to Gbps communication everywhere Faster deployment than terrestrial infrastructures Bypass clogged ...
| PowerPoint PPT presentation | free to view
Computer Networks Network layer Network Layer Design issues Routing Congestion Internetworking Internet Protocols Multimedia or QoS Different networks, protocols?
| PowerPoint PPT presentation | free to download
Network Analysis Diffusion Networks Social Network Philosophy Social structure is visible in an anthill Movements & contacts one sees are not random but patterned The ...
| PowerPoint PPT presentation | free to download
The Security Wheel: Defense In-Depth. Effective network security requires ... Fish Bowl or Honeypot -- Learn and record a hacker's knowledge of your network ...
| PowerPoint PPT presentation | free to view
Seeing Networks Barry Wellman, NetLab Department of Sociology University of Toronto wellman@chass.utoronto.ca ...
| PowerPoint PPT presentation | free to download
Boosting your blog's visibility requires strategic tactics. Focus on creating high-quality, engaging content tailored to your audience's interests and needs. Optimize your blog posts with relevant keywords and meta tags for better search engine rankings. Promote your blog across social media platforms, engage with your audience, collaborate with influencers, and guest post on reputable sites to expand your reach and increase visibility. To know more visit here https://singhimarketingsolutions.com/seo-services/mumbai/
| PowerPoint PPT presentation | free to download
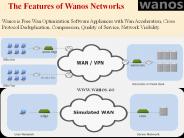
Wanos is Free Wan Optimization Software Appliances with Wan Acceleration, Cross Protocol Deduplication, Compression, Quality of Service, Network Visibility. See more @ http://wanos.co/wan-optimization/
| PowerPoint PPT presentation | free to download
North American Visibility
| PowerPoint PPT presentation | free to view
Using the Blockchain Technology, Zinc has created a Secure Recruitment and Hiring network to make hiring journey simple and smart for workers and recruiters within the technology sector.We are committed to creating a decentralised world, empowering freedom in all forms.
| PowerPoint PPT presentation | free to download
SOCIAL. NETWORKS. Amit Sharma. INF -38FQ. School of Information. University of Texas at Austin ... Social Networks. References. Everybody talks about Networks? ...
| PowerPoint PPT presentation | free to view
Community Seismic Network Daniel Obenshain along with K. Mani Chandy, Robert Clayton, Andreas Krause, Michael Olson, Matthew Faulkner, Leif Strand,
| PowerPoint PPT presentation | free to download
In its simplest form, a star network consists of one central hub, switch or ... Any non centralized failure will have very little effect on the network. ...
| PowerPoint PPT presentation | free to view
Rhino Labs Inc. provides quality products for network security systems and appliances. Rhino takes care of your hardware and applications run better. For more browse now. http://www.rhinolabsinc.com/
| PowerPoint PPT presentation | free to download
Data networks are not suitable for voice and video traffic because ... Host. ATM. Switch. ATM. Switch. ATM. Switch. NNI. NNI. UNI. NNI. UNI. Backbone Network. IFA'2005 ...
| PowerPoint PPT presentation | free to view
Find the reliable & trusted network monitoring center at Flight case. We deliver comprehensive service into network traffic management for accounting, Data analysis, reporting. There has been rapid technological change at very front, and network monitoring services are not an exception to it. Experts say that Network Monitoring Center service providers have to get adapted to the latest trends and maintaining profitability becomes incredibly difficult.
| PowerPoint PPT presentation | free to download
Data Communication and Networks Lecture 6 Networks: Part 1 Circuit Switching, Packet Switching, The Network Layer October 13, 2005 Switching Networks Long distance ...
| PowerPoint PPT presentation | free to download
Newest incarnation of social networking sites attempt to subsume: ... File sharing on social networks means collaborative filtering of bad files ...
| PowerPoint PPT presentation | free to view
Nothing's more regrettable than getting a call that the network is down. Time and again, IT does not have the visibility they have to advance beyond execution issues, which means you're oblivious until the point when a client or client calls to gripe. Once an outage happens, the clock is ticking. What's more, the more it takes to determine, the more it costs you: in staff time, lost profitability, and end-client fulfilment.
| PowerPoint PPT presentation | free to download
INTRANSIT VISIBILITY 50050011
| PowerPoint PPT presentation | free to view
Wireless Sensor Networks Market by Offering (Hardware, Software, Services), Sensor Type, Connectivity Type, End-user Industry (Building Automation, Wearable Devices, Healthcare, Automotive & Transportation, Industrial), and Region - Global Forecast to 2023
| PowerPoint PPT presentation | free to download
IP address: 32-bit identifier for host, router interface ... Banyan networks, other interconnection nets initially developed to connect ...
| PowerPoint PPT presentation | free to view
Microsoft Research, Cambridge (Guest lecture, Digital Communications II) ... Models of general communication networks. Tend to be quite abstract and ... technology ...
| PowerPoint PPT presentation | free to view
Advantages of Server-Based over Peer-to-Peer Networks ... In-depth knowledge of Microsoft networking products ... Microsoft Certified Systems Administrator (MCSA) ...
| PowerPoint PPT presentation | free to view
Goal 1: Create a set of core WSN management services to ensure constant visibility (the SNMS) ... Must create minimal network traffic when the network is healthy ...
| PowerPoint PPT presentation | free to view
ProActeye Activity Visibility is to ensure that no anomalous activities are going on in the organization.
| PowerPoint PPT presentation | free to download
Part 4: Network Layer CSE 3461/5461 Reading: Chapter 4, Kurose and Ross *
| PowerPoint PPT presentation | free to download
Still have hidden node prob. Use 4-way HS: Listen. Wait for IFS (50ms) ... Destination sends a CTS (visible to hidden node) Sender sends data ...
| PowerPoint PPT presentation | free to download
We at Refpay empower global Advertisers & Brands and Publishers of all sizes to grow their businesses online. Being a 360* solution-oriented performance company we are committed to meet your goals upon your trust on us. Refpay Media is now the leading solution-based digital marketing agency and an affiliate network headquartered in Singapore and India providing exemplary services to its clients. Refpay Media is a 360 degree performance driven platform that enables the brands to acquire the right audience to their destination. For More Details Visit :- https://www.refpaymedia.com/
| PowerPoint PPT presentation | free to download
Title: Redundant Network Architecture Author: Sunday Folayan Description: Material borrowed from Cisco Networkers presentations and Philip Smith Last modified by
| PowerPoint PPT presentation | free to download